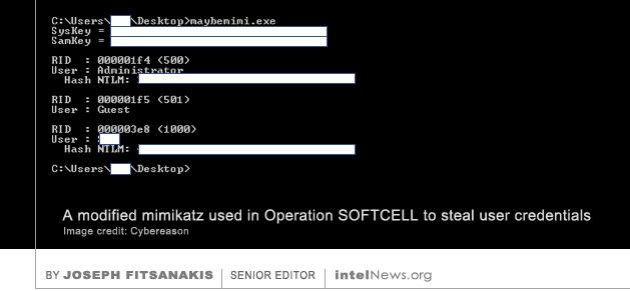
 A hacker attack of impressive magnitude targeted specific individuals of interest to the Chinese government as they moved around the world, in what appears to be the first such operation in the history of cyberespionage. The attack was revealed late last month by Cybereason, an American cybersecurity firm based in Boston, Massachusetts. Company experts described the scope and length of the attack, dubbed Operation SOFTCELL, as a new phenomenon in state-sponsored cyberespionage. Cybereason said SOFTCELL has been in operation since at least 2017, and identified the culprit as APT10, a hacker group that is believed to operate on behalf of China’s Ministry of State Security.
A hacker attack of impressive magnitude targeted specific individuals of interest to the Chinese government as they moved around the world, in what appears to be the first such operation in the history of cyberespionage. The attack was revealed late last month by Cybereason, an American cybersecurity firm based in Boston, Massachusetts. Company experts described the scope and length of the attack, dubbed Operation SOFTCELL, as a new phenomenon in state-sponsored cyberespionage. Cybereason said SOFTCELL has been in operation since at least 2017, and identified the culprit as APT10, a hacker group that is believed to operate on behalf of China’s Ministry of State Security.
The operation is thought to have compromised close to a dozen major global telecommunications carriers in four continents —the Middle East, Europe, Asia and Africa. According to Cybereason, the hackers launched persistent multi-wave attacks on their targets, which gave them “complete takeover” of the networks. However, they did not appear to be interested in financial gain, but instead focused their attention on the call detail records (CDRs) of just 20 network users. With the help of the CDRs, the hackers were able to track their targets’ movements around the world and map their contacts based on their telephone activity. According to The Wall Street Journal, which reported on Cybereason’s findings, the 20 targets consisted of senior business executives and government officials. Others were Chinese dissidents, military leaders, as well as law enforcement and intelligence officials.
An especially impressive feature of SOFTCELL was that the hackers attacked new telecommunications carriers as their targets moved around the world and made use of new service providers. The attacks thus followed the movements of specific targets around the world. Although this is not a new phenomenon in the world of cyberespionage, the geographical scope and persistence of the attacks are unprecedented, said The Wall Street Journal. Speaking last week at the 9th Annual International Cybersecurity Conference in Tel Aviv, Israel, Lior Div, Cybereason’s chief executive officer and co-founder, said SOFTCELL attacks occurred in waves over the course of several months. The hackers used a collection of techniques that are commonly associated with identified Chinese hacker groups. If detected and repelled, the hackers would retreat for a few weeks or months before returning and employing new methods. The Cybereason security experts said that they were unable to name the targeted telecommunications carriers and users “due to multiple and various limitations”.
► Author: Joseph Fitsanakis | Date: 09 July 2019 | Permalink
Attack by Chinese hacker group targeted high-profile individuals around the world
July 9, 2019 by Joseph Fitsanakis 2 Comments
The operation is thought to have compromised close to a dozen major global telecommunications carriers in four continents —the Middle East, Europe, Asia and Africa. According to Cybereason, the hackers launched persistent multi-wave attacks on their targets, which gave them “complete takeover” of the networks. However, they did not appear to be interested in financial gain, but instead focused their attention on the call detail records (CDRs) of just 20 network users. With the help of the CDRs, the hackers were able to track their targets’ movements around the world and map their contacts based on their telephone activity. According to The Wall Street Journal, which reported on Cybereason’s findings, the 20 targets consisted of senior business executives and government officials. Others were Chinese dissidents, military leaders, as well as law enforcement and intelligence officials.
An especially impressive feature of SOFTCELL was that the hackers attacked new telecommunications carriers as their targets moved around the world and made use of new service providers. The attacks thus followed the movements of specific targets around the world. Although this is not a new phenomenon in the world of cyberespionage, the geographical scope and persistence of the attacks are unprecedented, said The Wall Street Journal. Speaking last week at the 9th Annual International Cybersecurity Conference in Tel Aviv, Israel, Lior Div, Cybereason’s chief executive officer and co-founder, said SOFTCELL attacks occurred in waves over the course of several months. The hackers used a collection of techniques that are commonly associated with identified Chinese hacker groups. If detected and repelled, the hackers would retreat for a few weeks or months before returning and employing new methods. The Cybereason security experts said that they were unable to name the targeted telecommunications carriers and users “due to multiple and various limitations”.
► Author: Joseph Fitsanakis | Date: 09 July 2019 | Permalink
Filed under Expert news and commentary on intelligence, espionage, spies and spying Tagged with APT10, China, Cybereason, cyberespionage, cybersecurity, News, Operation SOFTCELL, telecommunication service providers