US Pentagon computers cannot be protected, says NSA head
January 13, 2012 3 Comments
 By JOSEPH FITSANAKIS | intelNews.org |
By JOSEPH FITSANAKIS | intelNews.org |
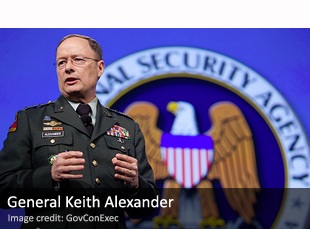
The man in charge of America’s most powerful intelligence agency says the United States Department of Defense computer network is so disordered and chaotic that it cannot be defended from cyberattacks. General Keith Alexander directs the National Security Agency, America’s wealthiest intelligence institution, which expert James Bamford has described as “the world’s most powerful spy agency”. As America’s foremost signals intelligence agency, the NSA is largely responsible for protecting the integrity, security and cohesion of the country’s public and restricted military communications networks, including computer networks. To do so, it consumes an annual budget that dwarfs those of most other intelligence agencies, and employs entire armies of computer security experts and other professionals. But, according to General Alexander, who also heads the US Pentagon’s new Cyber Command, there is not much his army of cyberwarriors can do to either prevent or repel possible large-scale cyberattacks directed against the DoD’s computer networks. The NSA chief was speaking yesterday at the International Conference on Cyber Security, a high-profile gathering of experts at New York’s Fordham University. He told the conference, which is sponsored by the Federal Bureau of Investigation, that the Pentagon’s computer infrastructure is too anarchic and chaotic to be successfully defended from cyberespionage, cyberterrorism, or cyberwarfare assaults. He said the DoD computer system consists of so many interconnected networks —over 15,000 in all— that the NSA “can’t see them all [let alone] defend them all”. As a result, said Alexander, the DoD’s current communications infrastructure “is indefensible”. In a separate but related development, unmanned Predator drones used by the US Central Intelligence Agency appear to have switched their computer navigation systems from Windows to Linux, after discovering a potentially disastrous computer virus on the previous system. The existence of the virus was publicly revealed in October by an article on Wired magazine’s Danger Room blog, which said that the virus surreptitiously recorded every keystroke made by the drones’ remote pilots. Now British-based technology review The Register reports that comparable photographs of drone control systems taken in 2009 and 2011 seem to show that the CIA’s new Predator remote control systems are Linux-based.







Reblogged this on @lissnup and commented:
Gary Manning’s defence lawyer needs to get General Alexander on the stand.
This is not “NEW” news, in 1991 as a Petty Officer First Class who was in charge of computer security for a Navy VP squadron (as a “Collateral Duty” not a full time job.) I went to a “Security Fair” as it was called at the time and one of the presenters said then; “As soon as all of the field commands local computer networks are interconnected with WAN links, the Navy will have built a beast that can not be made secure.” This was said in 1991, the argument then was that unless we tossed out all the Novell and Microsoft computer systems and required everyone to have a Unix biased Tempest complaint network, where all OS code comes from one place where it is Government Controlled we would never be able to secure it. The other view was that only an Operating System where everyone could see all the source code could ever have a hope of being made secure, because no company or government could provide the amount of scrutiny needed to find all the “flaws” in the code that would make it insecure. The only way to be sure that all possible exploits to be found was to give away an operating system to the world and let anyone use it and be able to look at the code, that way we could get “free” labor and the best minds we do not yet know about to find the flaws. Now I wonder, did Linux happen because of this or did this happen because of Linux? My point is we knew then…1991..that this day would come.
@B.D. Sawyer: Well, Linux development began in late 1990/early 1991, so the theory that the “Fair” you visited spawned Linux is probably wrong. Also, I disagree with the second view on OS security- that open source is more secure because it can be analyzed by many more experts for flaws. A truly secure OS would 1) Be closed sourced, 2) Provide no support for 3rd party drivers, and 3) Not allow ANY unsigned code to execute. There might be a 4th requirement, too, that is the OS would 4) Not connect to the Internet.