Russia says it uncovered U.S. operation to compromise Apple phones
June 2, 2023 1 Comment
 RUSSIAN OFFICIALS SAID THEY uncovered a sophisticated espionage effort by the United States government, which targeted the smartphones of thousands of Apple users living in Russia, including foreign diplomats. According to the Russians, the operation was carried out by the National Security Agency (NSA), an American intelligence agency that specializes in gathering foreign signals intelligence and securing the United States government’s information and communication systems.
RUSSIAN OFFICIALS SAID THEY uncovered a sophisticated espionage effort by the United States government, which targeted the smartphones of thousands of Apple users living in Russia, including foreign diplomats. According to the Russians, the operation was carried out by the National Security Agency (NSA), an American intelligence agency that specializes in gathering foreign signals intelligence and securing the United States government’s information and communication systems.
The source of the allegation is the Federal Security Service (FSB), Russia’s primary counterterrorism and counterintelligence agency. On Thursday, the FSB said that “an intelligence action of the American special services” had been uncovered by FSB officers with the assistance of the Federal Protective Service. Known in Russia by its initials, FSO, the Federal Protective Service operates federal emergency communications systems and provides personal security for high-ranking government officials.
According to the FSB, “several thousand Apple telephones” were targeted in the alleged NSA operation, including devices belonging to “domestic Russian subscribers”, as well as devices belonging to foreign diplomats stationed in Russia. The latter allegedly include diplomats from Israel, Syria and China, according to the FSB. The Russian agency also claimed that Russia-based foreign diplomats from North Atlantic Treaty Organization member-states had their phones targeted, as well as diplomats from former Soviet states.
In the same press release, the FSB accused the NSA and Apple of working in “close cooperation” with each other —an allegation that the Russian government has been making for several years. In a follow-up media statement, the Russian Ministry of Foreign Affairs accused the United States of engaging in “hidden data collection” and dismissed Apple iPhones as “absolutely transparent”.
Kremlin spokesman Dmitry Peskov urged Russians to avoid using Apple products and lamented reports that one in three Russian government workers continue to utilize Apple products for their personal use. When asked by reporters if the Russian government had plans to outlaw the use of Apple products by government employees, Peskov responded that the Kremlin did “not have the power to even recommend that”, except for those government employees with access to classified information.
► Author: Joseph Fitsanakis | Date: 02 June 2023 | Permalink
 UKRAINE IS INCREASINGLY RELIANT on its close intelligence relationship with the United States, which has grown dramatically in depth and intensity since Russia’s annexation of Crimea in 2014, according to a new report. The
UKRAINE IS INCREASINGLY RELIANT on its close intelligence relationship with the United States, which has grown dramatically in depth and intensity since Russia’s annexation of Crimea in 2014, according to a new report. The  THE FIRST CLAIMS OF an alleged secret collaboration between the signals intelligence agencies of the United States and Denmark surfaced in November of 2020. By January of this year, it was clear that the Danish government would, sooner or later, need to deal with the fallout of its controversial spy deal with Washington, under which Denmark enabled the US to spy on some of its closest European allies. Still, the
THE FIRST CLAIMS OF an alleged secret collaboration between the signals intelligence agencies of the United States and Denmark surfaced in November of 2020. By January of this year, it was clear that the Danish government would, sooner or later, need to deal with the fallout of its controversial spy deal with Washington, under which Denmark enabled the US to spy on some of its closest European allies. Still, the  AMERICA’S LARGEST SPY AGENCY, the National Security Agency, has reportedly placed on administrative leave its general counsel, who was installed on orders by the White House just hours before the end of Donald Trump’s presidency. Michael Ellis worked as an aide to Representative Devin Nunes (R-Ca) until 2017, when he joined the White House as the senior associate counsel to President Trump and deputy legal advisor to the National Security Council (NSC). In 2020 he was promoted to NSC’s senior director for intelligence.
AMERICA’S LARGEST SPY AGENCY, the National Security Agency, has reportedly placed on administrative leave its general counsel, who was installed on orders by the White House just hours before the end of Donald Trump’s presidency. Michael Ellis worked as an aide to Representative Devin Nunes (R-Ca) until 2017, when he joined the White House as the senior associate counsel to President Trump and deputy legal advisor to the National Security Council (NSC). In 2020 he was promoted to NSC’s senior director for intelligence.
 The director of America’s largest spy agency claims in a signed affidavit that a forthcoming book by John Bolton, President Donald Trump’s former national security adviser, would critically compromise intelligence secrets if published. Bolton served in that capacity from April 2018 until September 2019. His memoir of his time as President Trump’s national security advisor, titled
The director of America’s largest spy agency claims in a signed affidavit that a forthcoming book by John Bolton, President Donald Trump’s former national security adviser, would critically compromise intelligence secrets if published. Bolton served in that capacity from April 2018 until September 2019. His memoir of his time as President Trump’s national security advisor, titled  Switzerland is reeling from the shock caused by revelations last week that Crypto AG, the world’s leading manufacturer or cryptologic equipment during the Cold War, whose clients included over 120 governments around the world, was a front company owned by the United States Central Intelligence Agency.
Switzerland is reeling from the shock caused by revelations last week that Crypto AG, the world’s leading manufacturer or cryptologic equipment during the Cold War, whose clients included over 120 governments around the world, was a front company owned by the United States Central Intelligence Agency. Russian hackers hijacked an Iranian cyber espionage group and used its infrastructure to launch attacks, hoping that their victims would blame Iran, according to British and American intelligence officials. The information,
Russian hackers hijacked an Iranian cyber espionage group and used its infrastructure to launch attacks, hoping that their victims would blame Iran, according to British and American intelligence officials. The information, 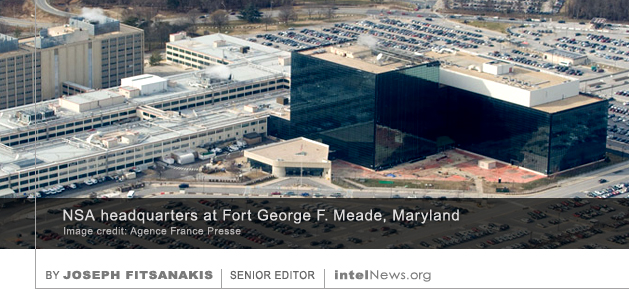 Representatives from the United States National Security Agency (NSA) withdrew a proposal to introduce new global industry standards for data encryption, after encountering prolonged skepticism by experts representing other Western countries. Some observers have interpreted this development as indicative of the damaged relationship between the NSA and its Western counterparts following revelations by American defector Edward Snowden.
Representatives from the United States National Security Agency (NSA) withdrew a proposal to introduce new global industry standards for data encryption, after encountering prolonged skepticism by experts representing other Western countries. Some observers have interpreted this development as indicative of the damaged relationship between the NSA and its Western counterparts following revelations by American defector Edward Snowden. The White House will soon announce its decision to strengthen the United States Cyber Command and separate cyber war operations from intelligence functions, according to insider reports. For many decades, the National Security Agency has been in charge of protecting America’s cyber network and combating online threats. But in 2009, the Administration of US President Barack Obama established a brand new Cyber Command, proposing that the online environment represented a new theater of war. Since that time, the US Department of Defense has been campaigning in favor of strengthening the new Cyber Command and completely removing it from the patronage of the NSA –despite the fact that the latter is also a Pentagon agency.
The White House will soon announce its decision to strengthen the United States Cyber Command and separate cyber war operations from intelligence functions, according to insider reports. For many decades, the National Security Agency has been in charge of protecting America’s cyber network and combating online threats. But in 2009, the Administration of US President Barack Obama established a brand new Cyber Command, proposing that the online environment represented a new theater of war. Since that time, the US Department of Defense has been campaigning in favor of strengthening the new Cyber Command and completely removing it from the patronage of the NSA –despite the fact that the latter is also a Pentagon agency. A lengthy parliamentary report on American intelligence activities in Germany was presented last week in Berlin, but was condemned by opposition parties as insufficient and incomplete, prompting calls for a new investigation. The parliamentary probe was initiated in 2013, following a series of
A lengthy parliamentary report on American intelligence activities in Germany was presented last week in Berlin, but was condemned by opposition parties as insufficient and incomplete, prompting calls for a new investigation. The parliamentary probe was initiated in 2013, following a series of  New information about carefully targeted attempts by Russian operatives to compromise the November 2016 presidential elections in the United States have emerged in a newly published intelligence document. The document, which dates from May of this year, was produced by the US National Security Agency and
New information about carefully targeted attempts by Russian operatives to compromise the November 2016 presidential elections in the United States have emerged in a newly published intelligence document. The document, which dates from May of this year, was produced by the US National Security Agency and  between leakers based on their motives. It does, however, distinguish between simple leakers and whistleblowers. If a US government employee uncovers evidence of abuse of power, or becomes aware of a specific and critical threat to the security of Americans, he or she is required to notify his or her superiors. If the latter refuse to take action, then the employee is justified under the law in taking all necessary actions to warn the public of impending peril. That is precisely the function of the 1989 Whistleblower Protection Act, which affords protection to insiders who expose abuses of authority, or a concrete and critical threat to public safety.
between leakers based on their motives. It does, however, distinguish between simple leakers and whistleblowers. If a US government employee uncovers evidence of abuse of power, or becomes aware of a specific and critical threat to the security of Americans, he or she is required to notify his or her superiors. If the latter refuse to take action, then the employee is justified under the law in taking all necessary actions to warn the public of impending peril. That is precisely the function of the 1989 Whistleblower Protection Act, which affords protection to insiders who expose abuses of authority, or a concrete and critical threat to public safety. 






NSA, CIA senior officials address artificial intelligence threats and opportunities
October 2, 2023 by Joseph Fitsanakis Leave a comment
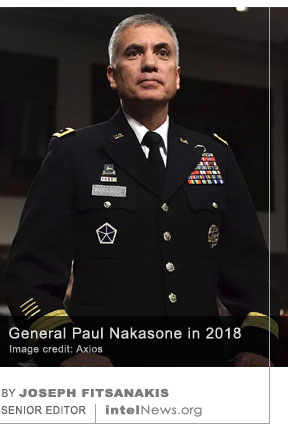
Nakasone (pictured) noted in his remarks that the US Intelligence Community, as well as the Department of Defense, have been using artificial intelligence for quite some time. Thus, artificial intelligence systems are already integral in managing and analyzing information on a daily basis. In doing so, such systems contribute in important ways to the decision-making by the NSA’s human personnel. At the same time, the NSA has been using artificial intelligence to develop and define best-practices guidelines and principles for intelligence methodologies and evaluation.
Currently, the United States maintains a clear advantage in artificial intelligence over is adversaries, Nakasone said. However, that advantage “should not be taken for granted”. As artificial intelligence organizational principles are increasingly integrated into the day-to-day functions of the intelligence and security enterprise, new risks are emerging by that very use. For this reason, the NSA has launched its new Artificial Intelligence Security Center within its existing Cybersecurity Collaboration Center. The mission of the Cybersecurity Collaboration Center is to develop links with the private sector in the US and its partner nations to “secure emerging technologies” and “harden the US Defense Industrial Base”.
Nakasone added that the decision to create the Artificial Intelligence Security Center resulted from an NSA study, which alerted officials to the national security challenges stemming from adversarial attacks against the artificial intelligence models that are currently in use. These attacks, focusing on sabotage or theft of critical artificial intelligence technologies, could originate from other generative artificial intelligence technologies that are under the command of adversarial actors.
Last Wednesday, the CIA’s Raman discussed some of the ways that artificial intelligence is currently being put to use by her agency to improve its analytical and operational capabilities. Raman noted that the CIA is developing an artificial intelligence chatbot, which is meant to help its analysts refine their research and analytical writing capabilities. Additionally, artificial intelligence systems are being used to analyze quantities of collected data that are too large for human analysts to manage. By devoting artificial intelligence resources to the relatively menial and low-level tasks of data-sifting and sorting, the CIA enables its analysts to dedicate more time to strategic-level products.
At the same time, however, the CIA is concerned about the rapid development of artificial intelligence by nations such as China and Russia, Raman said. New capabilities in artificial intelligence, especially the generative kind, will inevitably provide US adversaries with tools and capabilities that will challenge American national security in the coming years, she concluded.
► Author: Joseph Fitsanakis | Date: 02 October 2023 | Permalink
Filed under Expert news and commentary on intelligence, espionage, spies and spying Tagged with artificial intelligence, CIA, Lakshmi Raman, News, NSA, NSA Artificial Intelligence Security Center, NSA Cybersecurity Collaboration Center, Paul Nakasone, United States