June 17, 2021
by intelNews
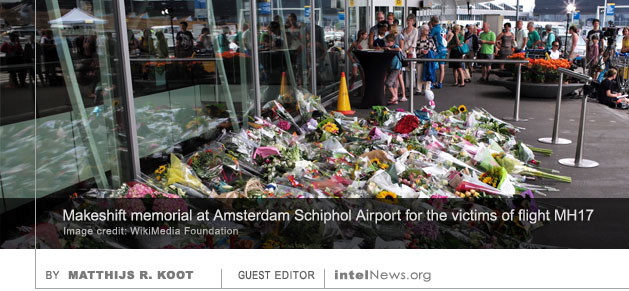
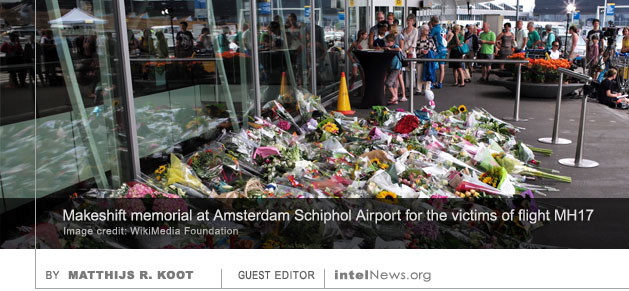
Russian hackers compromised the computer systems of the Dutch national police while the latter were conducting a criminal probe into the downing of Malaysia Airlines Flight 17 (MH17), according to a new report. MH17 was a scheduled passenger flight from Amsterdam to Kuala Lumpur, which was shot down over eastern Ukraine on July 17, 2014. All 283 passengers and 15 crew on board, 196 of them Dutch citizens, were killed.
Dutch newspaper De Volkskrant, which revealed this new information last week, said the compromise of the Dutch national police’s computer systems was not detected by Dutch police themselves, but by the Dutch General Intelligence and Security Service (AIVD). The paper said that neither the police nor the AIVD were willing to confirm the breach, but added that it had confirmed the breach took place through multiple anonymous sources.
On July 5, 2017, the Netherlands, Ukraine, Belgium, Australia and Malaysia announced the establishment of the Joint Investigation Team (JIT) into the downing of flight MH-17. The multinational group stipulated that possible suspects of the downing of flight MH17 would be tried in the Netherlands. In September 2017, the AIVD said it possessed information about Russian targets in the Netherlands, which included an IP address of a police academy system. That system turned out to have been compromised, which allowed the attackers to access police systems. According to four anonymous sources, evidence of the attack was detected in several different places.
The police academy is part of the Dutch national police, and non-academy police personnel can access the network using their log-in credentials. Some sources suggest that the Russian Foreign Intelligence Service (SVR) carried out the attack through a Russian hacker group known as APT29, or Cozy Bear. However, a growing number of sources claim the attack was perpetrated by the Main Directorate of the Russian Armed Forces’ General Staff, known commonly as GRU, through a hacker group known as APT28, or Fancy Bear. SVR attackers are often involved in prolonged espionage operations and are careful to stay below the radar, whereas the GRU is believed to be more heavy-handed and faster. The SVR is believed to be partly responsible for the compromise of United States government agencies and companies through the supply chain attack known as the SolarWinds cyber attack, which came to light in late 2020.
Russia has tried to sabotage and undermine investigation activities into the MH17 disaster through various means: influence campaigns on social media, hacking of the Dutch Safety Board, theft of data from Dutch investigators, manipulation of other countries involved in the investigation, and the use of military spies. The Dutch police and public prosecution service were repeatedly targeted by phishing emails, police computer systems were subjected to direct attacks, and a Russian hacker drove a car with hacking equipment near the public prosecution office in Rotterdam.
The above efforts are not believed to have been successful. But the attack that came to light in September 2017 may have been. The infected police academy system ran “exotic” (meaning uncommon) software, according to a well-informed source. The Russians reportedly exploited a zero day vulnerability in that software. After the incident, the national police made improvements in their logging and monitoring capabilities, and in their Security Operations Center (SOC). It is not currently known how long the attackers had access to the national police system, nor what information they were able to obtain.
► Author: Matthijs Koot | Date: 17 June 2021 | Permalink
 HACKERS HAVE COMPROMISED A website used by the United States Intelligence Community (IC) to solicit sensitive contracts from the private sector, according to a new report. The target of the attack, and the methods used by the hackers, appear to point with a high degree of certainty to a state actor.
HACKERS HAVE COMPROMISED A website used by the United States Intelligence Community (IC) to solicit sensitive contracts from the private sector, according to a new report. The target of the attack, and the methods used by the hackers, appear to point with a high degree of certainty to a state actor. MEMBERS OF A PROLIFIC hacker group that many associate with Russian intelligence impersonated Microsoft technicians in order to compromise nearly 40 government agencies and companies around the world. Microsoft security researchers
MEMBERS OF A PROLIFIC hacker group that many associate with Russian intelligence impersonated Microsoft technicians in order to compromise nearly 40 government agencies and companies around the world. Microsoft security researchers  AN ESPIONAGE TOOL DESCRIBED by Western officials as the most advanced in the Russian cyber-arsenal has been neutralized after a 20-year operation by intelligence agencies in the United States, Australia, Canada, the United Kingdom and New Zealand. The operation targeted
AN ESPIONAGE TOOL DESCRIBED by Western officials as the most advanced in the Russian cyber-arsenal has been neutralized after a 20-year operation by intelligence agencies in the United States, Australia, Canada, the United Kingdom and New Zealand. The operation targeted  A NOTORIOUS NORTH KOREAN hacker group is believed to be behind a “sophisticated” effort to elicit the views of international experts on issues that are of concern to Pyongyang, according to an investigation by Reuters. The news agency
A NOTORIOUS NORTH KOREAN hacker group is believed to be behind a “sophisticated” effort to elicit the views of international experts on issues that are of concern to Pyongyang, according to an investigation by Reuters. The news agency  A NEWLY DISCOVERED CYBER-espionage group appears to target the senior leadership of private corporations involved in large-scale financial transactions, but employs skills and methods that are usually associated with state-sponsored threat actors. The group has been termed “UNC3524” by the American cybersecurity firm Mandiant, which says it discovered it in December of 2019. In a detailed
A NEWLY DISCOVERED CYBER-espionage group appears to target the senior leadership of private corporations involved in large-scale financial transactions, but employs skills and methods that are usually associated with state-sponsored threat actors. The group has been termed “UNC3524” by the American cybersecurity firm Mandiant, which says it discovered it in December of 2019. In a detailed  RUSSIAN STATE COMPANIES, BUSINESSES and individuals are being targeted in an unprecedented wave of attacks by digital assailants, according to observers, who say they are surprised by its ferocity. Since February of this year, hackers have accessed the personal financial data of pro-Kremlin oligarchs, stolen millions of internal emails stored on Russian government severs, and defaced high-profile websites across the nation. The Washington Post, which
RUSSIAN STATE COMPANIES, BUSINESSES and individuals are being targeted in an unprecedented wave of attacks by digital assailants, according to observers, who say they are surprised by its ferocity. Since February of this year, hackers have accessed the personal financial data of pro-Kremlin oligarchs, stolen millions of internal emails stored on Russian government severs, and defaced high-profile websites across the nation. The Washington Post, which  ON MARCH 3, 2022, Dutch newspaper Volkskrant
ON MARCH 3, 2022, Dutch newspaper Volkskrant  THE NORTH KOREAN MISSILE program has developed rapidly in the past year, partly due to an influx of stolen cryptocurrency, which has now become “an important revenue source” for Pyongyang, according to a United Nations report. The confidential report was produced for the United Nations’ Security Council, by a committee tasked with monitoring the impact of the supranational body’s sanctions on the North Korean economy.
THE NORTH KOREAN MISSILE program has developed rapidly in the past year, partly due to an influx of stolen cryptocurrency, which has now become “an important revenue source” for Pyongyang, according to a United Nations report. The confidential report was produced for the United Nations’ Security Council, by a committee tasked with monitoring the impact of the supranational body’s sanctions on the North Korean economy. A HACKER WHO TARGETED a major Dutch-based reservations website has ties to intelligence agencies in the United States, according to a new report. The claim was made on Wednesday by three Dutch investigative journalists, Merry Rengers, Stijn Bronzwaer and Joris Kooiman. In a lengthy
A HACKER WHO TARGETED a major Dutch-based reservations website has ties to intelligence agencies in the United States, according to a new report. The claim was made on Wednesday by three Dutch investigative journalists, Merry Rengers, Stijn Bronzwaer and Joris Kooiman. In a lengthy 







Russian hacker group using Internet service providers to spy on foreign embassies
August 2, 2025 by Joseph Fitsanakis 3 Comments
Turla began its attempt to compromise a host of Russian internet service providers in February, according to Microsoft’s report. The group’s apparent goal has been to gain access to the software that enables Russian security agencies to legally intercept internet traffic, following the issuance of warrants by judges. This software is governed by Russia’s System for Operative Investigative Activities (SORM), which became law in 1995, under the presidency of Boris Yeltsin. All local, state, and federal government agencies in Russia use the SORM system to facilitate court-authorized telecommunications surveillance.
According to Microsoft, targeted Internet users receive an error message prompting them to update their browser’s cryptographic certificate. Consent by the user results in the targeted computer downloading and installing a malware. Termed ApolloShadow by Microsoft, the malware is disguised as a security update from Kaspersky, Russia’s most widely known antivirus software provider. Once installed the malware gives the hackers access to the content of the targeted user’s secure communications.
The Microsoft report states that, although Turla has been involved in prior attacks against diplomatic targets in Russia and abroad, this is the first time that the hacker group has been confirmed to have the capability to attack its targets at the Internet Service Provider (ISP) level. In doing so, Turla has been able to incorporate Russia’s domestic telecommunications infrastructure into its attack tool-kit, the report states. The report does not name the diplomatic facilities or the countries whose diplomats have been targeted by Turla hackers. But it warns that all “diplomatic personnel using local [internet service providers] or telecommunications services in Russia are highly likely targets” of the group.
► Author: Joseph Fitsanakis | Date: 02 August 2025 | Permalink
Filed under Expert news and commentary on intelligence, espionage, spies and spying Tagged with ApolloShadow, computer hacking, cyberespionage, diplomatic security, Moscow, News, Russia, Secret Blizzard, Snake malware, SORM (Russia), System for Operative Investigative Activities (Russia), Turla