Trump chief of staff’s phone was breached for nearly a year, say sources
October 9, 2017 4 Comments
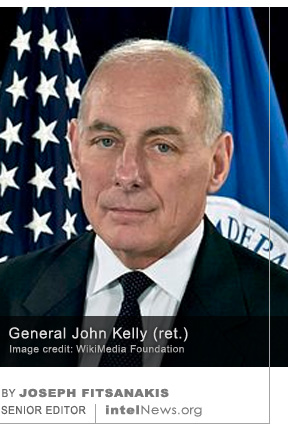 The personal cell phone of the White House Chief of Staff John Kelly (photo) was compromised by persons unknown and may have been bugged for nearly a year, according to United States government officials. General Kelly retired from the US Marine Corps in 2016, after serving as chief of the US Pentagon’s Southern Command, where he supervised American military operations in Latin America and the Caribbean. Soon afterwards, he was appointed by US President Donald Trump to lead the Department of Homeland Security, which he joined in January of 2017. Six months later, however, he replaced Reince Priebus, who resigned abruptly from the post of White House Chief of Staff, citing differences over management style with the Trump administration.
The personal cell phone of the White House Chief of Staff John Kelly (photo) was compromised by persons unknown and may have been bugged for nearly a year, according to United States government officials. General Kelly retired from the US Marine Corps in 2016, after serving as chief of the US Pentagon’s Southern Command, where he supervised American military operations in Latin America and the Caribbean. Soon afterwards, he was appointed by US President Donald Trump to lead the Department of Homeland Security, which he joined in January of 2017. Six months later, however, he replaced Reince Priebus, who resigned abruptly from the post of White House Chief of Staff, citing differences over management style with the Trump administration.
According to the online news outlet Politico, the breach of Kelly’s personal phone was discovered last summer, after the retired general sought the advice of the White House’s technical support staff. Kelly told the technical experts that his phone’s operating system had been malfunctioning for several months and that software updates seemed to make the problem worse. Once the breach was discovered, White House staff summarized the findings of the probe into Kelly’s phone in a one-page memorandum. Three people who read the document spoke anonymously to Politico. The news outlet said that, according to the White House memorandum, it is unclear how and when Kelly’s phone was breached. There is also no information in the document about how much and what kind of information was compromised throughout the duration of the breach. Politico cited a White House spokesman who claimed that the chief of staff used his personal phone sparsely and never for government business.
However, depending on the level of the breach, hackers could have used the compromised phone to listen in to Kelly’s private conversations —in and out of the White House— even when the phone was not in use but simply turned on. It follows that if the breach of Kelly’s phone was orchestrated by a foreign government, the magnitude of the compromise may be substantial. Politico reports that digital forensics experts are now reviewing Kelly’s travels in the past year, as part of a widening investigation into the breach. Meanwhile, the general has been issued a new phone for his personal use.
► Author: Joseph Fitsanakis | Date: 10 October 2017 | Permalink







One hopes that the “breach of Kelly’s personal phone…discovered last summer” was detected by NSA officers working on the Information Assurance mission. https://www.nsa.gov/what-we-do/information-assurance/
Still, loopholes exist that hostile foreign intelligence agencies can exploit. That is the NSA is oriented to protecting “systems that handle classified information or are otherwise critical to military or intelligence activities”. http://www.nsa.gov/what-we-do/information-assurance/
with less emphasis on theoreticly “unclassified” cell phones.
Problems relating to a high level government figure’s unclassified cell phone are not only potential use as an audio microphone (as you article indicates).
I would say a cell phone could also be used by a hostile intelligence agency to:
– intercept personal computer emissions
– use the camera function to serve as a video device for photographing text on classified documents
– and act as a GPS tracking device.
@Pete: Good comment. Important subject matter. TEMPEST attacks are more common than people suspect.
Thanks “Jones”
And the risk of interception of low TEMPEST rated [1] computers has been around for decades – and now includes laptops.
Such interception is a real risk in any Russian, Chinese (or other foreign) hacking attack against US officials and their databases. This would all be part of the Mueller (on the surface FBI but also more quietly NSA) investigation [2]
[1] https://en.wikipedia.org/wiki/Tempest_(codename)
[2] See last paragraph of this https://en.wikipedia.org/wiki/2017_Special_Counsel_investigation#Obstruction_of_justice subsection
Government officials use of personal smart phones or other electronic communication devices (E.C.D.) today are equally vulnerable to cyber attacks – if not harden. Off the shelf E.C.D. provide soft vector targets for state actors, hacktivist, etc., to exploit.
Protecting electronic communications devices office/home is not sole domain of cyber security or IT professionals. Consumers of these devices must be proactive in also protecting their own privacy – which is a challenge, but not insurmountable.
Even if one supposedly has nothing to hide – they are not looking at the bigger picture. Some might not care, but one’s company might if phone gets hacked, lost or stolen and is not secure.
October is National Cybersecurity Awareness Month
Also:
Bruce Schneier who discusses security issues, recently discussed topic concerning “compromise” of John Kelly’s cell phone.
“I know this is news because of who he is, but I hope every major government official of any country assumes that their commercial off-the-shelf cell phone is compromised. Even allies spy on allies; …………”