Comment: Who authored computer virus that ‘dwarfs Stuxnet’?
June 6, 2012 9 Comments
 By JOSEPH FITSANAKIS | intelNews.org |
By JOSEPH FITSANAKIS | intelNews.org |
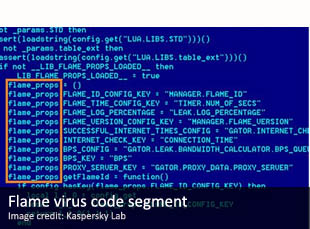
When the Stuxnet computer virus was detected, in 2010, it was recognized as the most sophisticated malware ever created. It had been specifically designed to sabotage Siemens industrial software systems, which were used in Iran’s nuclear energy program. Not surprisingly, most Stuxnet-infected computers were in Iran. Now a new, massive and extremely sophisticated piece of malware has been detected in computers belonging to the Iranian National Oil Company and Iran’s Ministry of Petroleum. It is called Flame and, according to antivirus company Kaspersky Lab, which first spotted the virus last week, it is “one of the most complex threats ever discovered”. Simply consider that Stuxnet, which caused unprecedented waves of panic among Iranian cybersecurity experts, was 500 kilobytes in size. Flame is over 20 megabytes in size, consisting of 650,000 lines of code; it is so complex that it is expected to take programming analysts around a decade to fully comprehend. The two are different, of course. Stuxnet was an infrastructure-sabotaging malware, which destroyed hundreds —maybe even thousands—of Iranian nuclear centrifuges. Flame, on the other hand, appears to be an espionage tool: it aims to surreptitiously collect information from infected systems. What connects them is their intended target: Iran. We now have Stuxnet, the most complex sabotaging malware ever discovered, which must have taken dozens of programmers several months to create, and Flame, the world’s most powerful cyberespionage tool ever detected by computer security experts. And both have been primarily directed at Iranian government computers.
As far as this commentator is concerned, the question at this point is not whether Flame emerged from a state-sponsored cyberespionage operation. This should be taken as given. The question is whether the massive malware is a product of an Israeli, an American, or an Israeli-American team of computer programmers (note: the possibility of a collaborative secret effort by a host of Western countries and Israel –something like a cyberwar version of the Manhattan Project– should not be overlooked). On May 29, shortly after the announcement of Flame’s discovery by Kaspersky, Israeli Vice Prime Minister and Minister of Strategic Affairs, Moshe Ya’along, hinted that Israel may have been behind the malware, saying that “Israel is blessed to be a nation possessing superior technology, [which] opens up all kinds of possibilities”. Later that day, however, MSNBC cited an unnamed American official, who claimed that Washington was responsible for the malware.
It is worth pointing out that the claim by MSNBC was eventually backed by Israeli sources. It is also worth considering that some Israelis have gone as far as to suggest that Israel, along with Iran, was also targeted by Flame, and thus could not have been the source of the virus. This is a valid point. Over 100 computers are thought to have been infected by Flame in Israel, second-only to Iran’s 198. Other countries targeted include Lebanon, Syria, and Sudan. Before drawing firm conclusions, however, one would have to have precise information as to the precise ownership of infected computer systems. For instance, are the infected computers in Israel proper, or in the Occupied Territories? Do the infected systems in Lebanon belong to the Lebanese government, or to Hezbollah? When were the computers in Syria infected? Are there any infected systems in the United States? Pakistan? China? If there are, will we ever find out about them?
Regardless of the answers to the above questions, there is no little doubt that Flame’s handlers have collected massive amounts of intelligence for at least two years. The program was apparently able to record conversations conducted over Skype; take desktop snapshots every 15 seconds or so; and collect usernames and passwords, among other capabilities. And all that while circumventing even the strongest antivirus software. But there is also the other side of the equation: as in the case of Stuxnet, Flame is now effectively freeware. Anyone can ostensibly access it, copy it, modify it, and re-launch it against his or her target of choice –even the United States, or Israel. This is comparable to winning a battle with the help of a brand new and exclusive weapon, and then proceeding to share its blueprints with the entire world. This policy may be arguably preventing a direct military confrontation with Iran; but it is clearly detrimental to international security as a whole.







What goes around comes around.
The only ones capable are the Red Team, NSA or the Israeli’s I put my money on the israeli’s from the “Bunker” in Tel Aviv.
After hearing for years that China was the most active or ‘threateneing’ user of hackers/sigint it is refreshing to hear that (hopefully) the US and or Israel have produced and are using Flame. Who said the US was declining?
On “is no little doubt that Flame’s handlers have collected massive amounts of intelligence for at least two years.” I recommend readers have a look at the first few paras of http://www.wired.com/threatlevel/2012/04/shady-companies-nsa/all/1 regarding the NSA’s massive expansion plans in terms of 1,000s of “intercept operators” and huge growth in computer capacity to handle the inflow of signals intelligence.
What I’m suggesting is that Flame as an intelligence collection multiplier needs the manpower and computer capacity to best utilize it. It very much looks as though NSA is expanding to handle that volume. Further supporting the Flame tie-up – in the (wired) article also see the very close “cross interception” (mutual “bugging”) relationship developing between US and Israeli sigint agencies and contractors.
Pete
(from Australia)
If it does take a decade to analyze Flame then by the end of that time there will already be a better an newer version or a complete new virus more robust that is already for some time on the Internet and infiltrated everywhere. Maybe even now?
@Pete: Excellent comment, and thanks. Completely agree on the manpower needed to handle the intercepted data, hence the obvious link to a nation-state. In regards to your first sentence, please see one of my earlier articles on the subject, here.
@AlbertE: Good point. I meant to suggest that, if programmers wanted to analyze Flame, it would take a large company 10 years of dedication to do so to the maximum extent. Not that they would necessarily do that. [JF]
Thanks Joseph
I’ve long suspected the NSA was not merely passive in fielding (mainly?) Chinese cyberattacks. Your May-June 2012 articles have proven very useful in filling the informational and attitudinal void about the NSA’s proactive moves.
I’m aware that surveillance software to turn home or office computers into audio-visual ‘bugging’ devices have been operated by security services in developed countries for at least a decade. This limited NSA, FBI (and also CIA for foreign ops) capability has now blossomed into vastly more comprehensive Flame ‘malware’ for security purposes and also secret intelligence collection.
I’m assuming the NSA has developed a comprehensive range of surveillance/collection software packages that remain ‘black’ – with Flame a partially known tip of the iceberg.
Pete
@Pete: Thanks for your comment. My personal view is that the unprecedented rise in technical surveillance measures (i.e. remote computer hacking and related arts) is directly proportional to the increasing difficulty of safely conducting HUMINT in today’s challenging intelligence landscape. [JF]
The need for such a defense, from entities that are hostile to global concerns, must rest in the hands of responsible concerns. With the few, those who seek global immolation with their self serving destructive tactics, unfortunately, this is today’s reality. I would hope and pray that we all can come together and unite in peace and live in harmony. Until then, this is the world we have to contend with.
May I add, that the price for freedom has become that more expensive.