Lax security behind greatest data loss in CIA’s history, internal report concludes
June 17, 2020 1 Comment
 Complacency and substandard security by the United States Central Intelligence Agency were behind the Vault 7 leak of 2017, which ranks as the greatest data loss in the agency’s history, according to an internal report. The Vault 7 data loss was particularly shocking, given that the CIA should have taken precautions following numerous leaks of classified government information in years prior to 2017, according to the report.
Complacency and substandard security by the United States Central Intelligence Agency were behind the Vault 7 leak of 2017, which ranks as the greatest data loss in the agency’s history, according to an internal report. The Vault 7 data loss was particularly shocking, given that the CIA should have taken precautions following numerous leaks of classified government information in years prior to 2017, according to the report.
The Vault 7 data leak occurred in the first half of 2017, when the anti-secrecy website WikiLeaks began publishing a series of technical documents belonging to the CIA. Once all documents had been uploaded to the WikiLeaks website, they amounted to 34 terabytes of information, which is equivalent to 2.2 billion pages of text. The information contained in the Vault 7 leak is believed to constitute the biggest leak of classified data in the history of the CIA.
The Vault 7 documents reveal the capabilities and operational details of some of the CIA’s cyber espionage arsenal. They detail nearly 100 different software tools that the agency developed and used between 2013 and 2016, in order to compromise targeted computers, computer servers, smartphones, cars, televisions, internet browsers, operating systems, etc. In 2017 the US government accused Joshua Adam Schulte, a former CIA software engineer, of giving the Vault 7 data to WikiLeaks. Schulte’s trial by jury was inconclusive, and a re-trial is believed to be in the works.
Now an internal report into the Vault 7 disclosure has been made public. The report was compiled by the CIA WikiLeaks Task Force, which the agency set up with the two-fold mission of assessing the damage from the leak and recommending security procedures designed to prevent similar leaks from occurring in the future. A heavily redacted copy of the report has been made available [.pdf] by Senator Ron Wyden (D-OR) who is a member of the US Senate Select Committee on Intelligence. An analysis of the report was published on Tuesday by The Washington Post.
The report recognizes that insider threats —a data leak perpetrated on purpose by a conscious and determined employee, or a group of employees— are especially difficult to stop. It adds, however, that the Vault 7 leak was made easier by “a culture of shadow IT” in which the CIA’s various units developed distinct IT security practices and their own widely different systems of safeguarding data. Many cyber units prioritized creative, out-of-the-box thinking, in order to develop cutting-edge cyber-tools. But they spent hardly any time thinking of ways to safeguard the secrecy of their projects, and failed to develop even basic counterintelligence standards —for instance keeping a log of which of their members had access to specific parts of the data— according to the report.
Such standards should have been prioritized, the report adds, given the numerous high-profile leaks that rocked the Intelligence Community in the years prior to the Vault 7 disclosure. It mentions the examples of Edward Snowden, a former contractor for the National Security Agency, who defected to Russia, as well as Chelsea Manning, an intelligence analyst for the US Army, who gave government secrets to WikiLeaks. Manning spent time in prison before being pardoned by President Barack Obama. Snowden remains in hiding in Russia.
The CIA has not commented on the release of the internal Vault 7 report. An agency spokesman, Timothy Barrett, told The New York Times that the CIA was committed to incorporating “best-in-class technologies to keep ahead of and defend against ever-evolving threats”. In a letter accompanying the release of the report, Senator Wyden warned that “the lax cybersecurity practices documented in the CIA’s WikiLeaks task force report do not appear limited to just one part of the intelligence community”.
► Author: Joseph Fitsanakis | Date: 17 June 2020 | Permalink
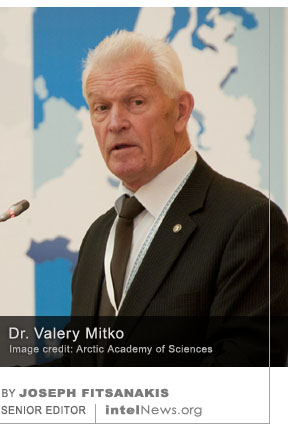 Russian prosecutors have accused one of the country’s most respected hydroacoustics specialists, and globally recognized expert on the Arctic region, of spying for Chinese intelligence. This development highlights the competitive relationship between the two neighboring countries, who in recent years have tended to work together against what they perceive as a common threat coming from the United States.
Russian prosecutors have accused one of the country’s most respected hydroacoustics specialists, and globally recognized expert on the Arctic region, of spying for Chinese intelligence. This development highlights the competitive relationship between the two neighboring countries, who in recent years have tended to work together against what they perceive as a common threat coming from the United States. Researchers at a university in Israel claim to have discovered a new low-tech eavesdropping technique, which relies on sound vibrations on the glass surface of light bulbs and requires equipment costing less than $1,000. The researchers claim that the technique, which they call “lamphone”, enables eavesdroppers to intercept, in real time, audible conversations from a room located hundreds of feet away, simply by recording the vibrations that sounds create on the glass surface of a common light bulb present in the room.
Researchers at a university in Israel claim to have discovered a new low-tech eavesdropping technique, which relies on sound vibrations on the glass surface of light bulbs and requires equipment costing less than $1,000. The researchers claim that the technique, which they call “lamphone”, enables eavesdroppers to intercept, in real time, audible conversations from a room located hundreds of feet away, simply by recording the vibrations that sounds create on the glass surface of a common light bulb present in the room. • French forces kill al-Qaeda head and capture ISIS leader in Mali. In the past few days, the French military
• French forces kill al-Qaeda head and capture ISIS leader in Mali. In the past few days, the French military  • UN report says Afghan Taliban still maintain ties with al-Qaida. The Taliban in Afghanistan still maintain close ties with the al-Qaida terror network, despite signing a peace deal with the United States in which they committed to fight militant groups, a UN
• UN report says Afghan Taliban still maintain ties with al-Qaida. The Taliban in Afghanistan still maintain close ties with the al-Qaida terror network, despite signing a peace deal with the United States in which they committed to fight militant groups, a UN  A court in Austria has found a retired Army colonel guilty of providing classified military information to Russia, following a closed-door trial. Interestingly, the alleged spy’s name has not been made public. Some Austrian media have been referring to him as “Martin M.”.
A court in Austria has found a retired Army colonel guilty of providing classified military information to Russia, following a closed-door trial. Interestingly, the alleged spy’s name has not been made public. Some Austrian media have been referring to him as “Martin M.”. Members of neo-Nazi groups in Germany attended paramilitary training camps in Russia, which were organized by a group that the United States has designated a global terrorist organization, but which the Russian government has not banned. If true, these claims add further credence to the view that Russian far-right groups are becoming increasingly central in the worldwide network of racially motivated radical organizations.
Members of neo-Nazi groups in Germany attended paramilitary training camps in Russia, which were organized by a group that the United States has designated a global terrorist organization, but which the Russian government has not banned. If true, these claims add further credence to the view that Russian far-right groups are becoming increasingly central in the worldwide network of racially motivated radical organizations. Moscow has reacted angrily to the Czech government’s decision to expel two Russian diplomats from the country, in response to allegations that the Kremlin plotted to assassinate three outspoken Czech politicians using a deadly poison. Russian officials pledged to respond in kind to Prague’s “indecent and unworthy deed”.
Moscow has reacted angrily to the Czech government’s decision to expel two Russian diplomats from the country, in response to allegations that the Kremlin plotted to assassinate three outspoken Czech politicians using a deadly poison. Russian officials pledged to respond in kind to Prague’s “indecent and unworthy deed”. The United States Defense Intelligence Agency, a Pentagon organization tasked with collecting foreign military secrets, has rejected reports that it is spying on protestors inside the country. However, it confirmed that it has set up an “internal coordination group” to respond to “requests for information” by the Department of Defense. This development follows reports that some DIA employees communicated their concerns about being asked to spy domestically to the organization’s director last week.
The United States Defense Intelligence Agency, a Pentagon organization tasked with collecting foreign military secrets, has rejected reports that it is spying on protestors inside the country. However, it confirmed that it has set up an “internal coordination group” to respond to “requests for information” by the Department of Defense. This development follows reports that some DIA employees communicated their concerns about being asked to spy domestically to the organization’s director last week. • State-level espionage on EU a ‘very high threat’ says report. The most successful attempts of espionage at a top EU institution are state sponsored, according to an
• State-level espionage on EU a ‘very high threat’ says report. The most successful attempts of espionage at a top EU institution are state sponsored, according to an  • Australian spy agency seeks expanded powers. The Australian Security Intelligence Organisation (ASIO) says it needs
• Australian spy agency seeks expanded powers. The Australian Security Intelligence Organisation (ASIO) says it needs  The embassy of the United States in the United Arab Emirates declined free COVID-19 testing kits for its staff, because of concerns that the private labs offering the kits had ties to China, according to a new report. The testing kits were offered by a testing facility that was set up in March in Abu Dhabi, which is the capital of the oil-rich UAE —a close American ally in the Middle East.
The embassy of the United States in the United Arab Emirates declined free COVID-19 testing kits for its staff, because of concerns that the private labs offering the kits had ties to China, according to a new report. The testing kits were offered by a testing facility that was set up in March in Abu Dhabi, which is the capital of the oil-rich UAE —a close American ally in the Middle East. In a recent video message, the new head of the Islamic State calls COVID-19 a “great torment” from God against unbelievers, and vows that “not a single day will pass without bloodshed” due to attacks by his forces. The 39-minute video is entitled “The Crusaders Will Know Who Will Win in the End”, and began to circulate on the popular messaging application Telegram last Thursday.
In a recent video message, the new head of the Islamic State calls COVID-19 a “great torment” from God against unbelievers, and vows that “not a single day will pass without bloodshed” due to attacks by his forces. The 39-minute video is entitled “The Crusaders Will Know Who Will Win in the End”, and began to circulate on the popular messaging application Telegram last Thursday. The former president of Argentina, Mauricio Macri, has been indicted as part of a widening investigation into a domestic spying program, which allegedly targeted opposition politicians, journalists and other public figures. The alleged espionage took place between 2015 and 2019, when Macri occupied the country’s highest office.
The former president of Argentina, Mauricio Macri, has been indicted as part of a widening investigation into a domestic spying program, which allegedly targeted opposition politicians, journalists and other public figures. The alleged espionage took place between 2015 and 2019, when Macri occupied the country’s highest office.






Cybersecurity researchers uncover first-ever use of LinkedIn to spread malware
June 18, 2020 by Joseph Fitsanakis Leave a comment
The existence of the alleged cyberespionage operation was revealed on Wednesday by researchers at ESET, a cybersecurity firm based in Bratislava, Slovakia, which is known for its firewall and anti-virus products. The researchers said that the operation was carried out in 2019 by hackers who impersonated employees of General Dynamics and Collins Aerospace, two leading global suppliers of aerospace and defense hardware.
ESET researchers said that the hackers made use of the private messaging feature embedded in LinkedIn to reach out to their targets. After making initial contact with their intended victims, the hackers allegedly offered their targets lucrative job offers and used the LinkedIn private messenger service to send them documents that were infected with malware. In many cases, the targets opened the documents and infected their computers in the process.
The use of the LinkedIn social media platform by hackers to make contact with their unsuspecting victims is hardly new. In 2017, German intelligence officials issued a public warning about what they said were thousands of fake LinkedIn profiles created by Chinese spies to gather information about Western targets. Germany’s Federal Office for the Protection of the Constitution (BfV) said it had identified 10,000 German citizens who had been contacted by Chinese spy-run fake profiles on LinkedIn in a period of just nine months. And in 2018, a report by France’s two main intelligence agencies, the General Directorate for Internal Security (DGSI) and the General Directorate for External Security (DGSE), warned of an “unprecedented threat” to security after nearly 4,000 leading French civil servants, scientists and senior executives who were found to have been accosted by Chinese spies on LinkedIn.
Tricking a target into accessing a virus-infected document file is not a new method either. However, according to the researchers at ESET, this was the first case where LinkedIn was used to actually deliver the malware to the victims. As for the identity of the hackers, there appears to be no concluding information. However, ESET said the attacks appeared to have some connections to Lazarus, a group of hackers with North Korean links. Lazarus has been linked to the 2014 Sony Pictures hack and the 2016 Central Bank of Bangladesh cyber heist, which was an attempt to defraud the bank of $1 billion.
LinkedIn told the Reuters news agency that it had identified and terminated the user accounts behind the alleged cyberespionage campaign. Citing client confidentiality, ESET said it could not reveal information about the victims of the attacks. Meanwhile, General Dynamics and Raytheon Technologies, which owns Collins Aerospace, have not commented on this report.
► Author: Joseph Fitsanakis | Date: 18 June 2020 | Permalink
Filed under Expert news and commentary on intelligence, espionage, spies and spying Tagged with Collins Aerospace, cyberespionage, ESET, General Dynamics, Lazarus, LinkedIn, News, Raytheon Corporation