Analysis: A look at the CIA’s half-century-old ‘disease intelligence’ program
June 22, 2020 Leave a comment
 The general discussion about how and when the White House was alerted by its spy agencies about COVID-19, points to the existence of ‘disease intelligence’ programs in the United States Intelligence Community. Relatively little is known about the history and current state of these programs. Last weekend, however, ABC News’ investigative correspondent Lee Ferran brought to light an article from 48 years ago in a declassified intelligence publication that sheds light on the roots of the Central Intelligence Agency’s disease intelligence effort.
The general discussion about how and when the White House was alerted by its spy agencies about COVID-19, points to the existence of ‘disease intelligence’ programs in the United States Intelligence Community. Relatively little is known about the history and current state of these programs. Last weekend, however, ABC News’ investigative correspondent Lee Ferran brought to light an article from 48 years ago in a declassified intelligence publication that sheds light on the roots of the Central Intelligence Agency’s disease intelligence effort.
The article was published in the declassified edition of Studies in Intelligence, the CIA’s in-house research publication. Written by Warren F. Carey and Myles Maxfield, the article appeared [.pdf] in the spring 1972 issue of the journal, and is titled “Intelligence Implications of Disease”. It discusses the 1966 outbreak of meningitis in China’s Guangdong Province, which prompted the CIA to begin tracking diseases in a systematic way. The outbreak first appeared in the city that is today known as Guangzhou, and within weeks it had resulted in a military takeover of the Chinese healthcare system. The latter collapsed in places, and prompted the CIA’s Office of Scientific Intelligence (known today as the Directorate of Science and Technology) to begin collecting data in order to assess the political fallout of the disease.
The article states that the CIA cryptonym for the disease was Project IMPACT. Its scope was limited, but it expanded 1968, when the world health community began to issue alerts about the so-called Hong Kong flu. Known officially as Hong Kong/A2/68, the virus spread around the world in a few months, and is believed to have killed between 1 and 4 million people, including around 100,000 Americans. At that time, according to the article in Studies in Intelligence, the CIA’s Project IMPACT “went global”, and was combined with BLACKFLAG, an ongoing effort by the Agency to “computerize disease information and derive trends, cycles and predictions” on a global scale.
Project BLACKFLAG tracked the spread of the disease in the Soviet Union and in North Vietnam, and issued regular analyses of the political ramification of the epidemic. That was not easy, say the authors, given the fact that most nations of the communist bloc tried to conceal information about it. The CIA was also able to issue warnings to its teams of operatives abroad, instructing them to shield themselves from the flu as it spread around East Asia and, eventually, the world.
According the authors, the CIA’s early disease intelligence projects were able to demonstrate that data aggregation was critical in helping monitor and forecast outbreaks. It also showed that these such forecasts could have “an initiating and vital role” in political, military and economic intelligence. Today, says Ferran, the CIA’s disease intelligence program has the same twofold mission it had when it was first conceived: first, to collect intelligence about the actual extent of the spread of diseases abroad —which may differ from the official information provided by foreign governments; and second, to try to forecast the consequences of these trends for American interests in the regions impacted by an ongoing epidemic or pandemic.
► Author: Joseph Fitsanakis | Date: 22 June 2020 | Permalink
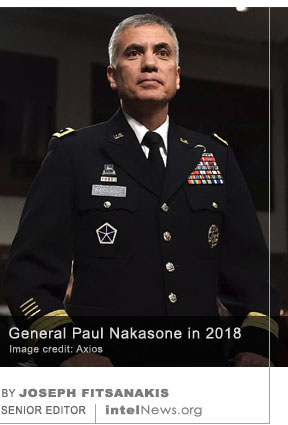 The director of America’s largest spy agency claims in a signed affidavit that a forthcoming book by John Bolton, President Donald Trump’s former national security adviser, would critically compromise intelligence secrets if published. Bolton served in that capacity from April 2018 until September 2019. His memoir of his time as President Trump’s national security advisor, titled
The director of America’s largest spy agency claims in a signed affidavit that a forthcoming book by John Bolton, President Donald Trump’s former national security adviser, would critically compromise intelligence secrets if published. Bolton served in that capacity from April 2018 until September 2019. His memoir of his time as President Trump’s national security advisor, titled  Cybersecurity researchers have uncovered what is believed to be the first-ever case of hackers using LinkedIn to infect the computers of targeted users with viruses, according to a new report. The hackers appear to have been sponsored by government and to have targeted employees of carefully selected military contractors in central Europe, according to sources.
Cybersecurity researchers have uncovered what is believed to be the first-ever case of hackers using LinkedIn to infect the computers of targeted users with viruses, according to a new report. The hackers appear to have been sponsored by government and to have targeted employees of carefully selected military contractors in central Europe, according to sources. Complacency and substandard security by the United States Central Intelligence Agency were behind the Vault 7 leak of 2017, which ranks as the greatest data loss in the agency’s history, according to an internal report. The Vault 7 data loss was particularly shocking, given that the CIA should have taken precautions following numerous leaks of classified government information in years prior to 2017, according to the report.
Complacency and substandard security by the United States Central Intelligence Agency were behind the Vault 7 leak of 2017, which ranks as the greatest data loss in the agency’s history, according to an internal report. The Vault 7 data loss was particularly shocking, given that the CIA should have taken precautions following numerous leaks of classified government information in years prior to 2017, according to the report.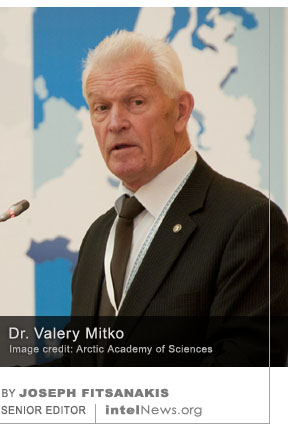 Russian prosecutors have accused one of the country’s most respected hydroacoustics specialists, and globally recognized expert on the Arctic region, of spying for Chinese intelligence. This development highlights the competitive relationship between the two neighboring countries, who in recent years have tended to work together against what they perceive as a common threat coming from the United States.
Russian prosecutors have accused one of the country’s most respected hydroacoustics specialists, and globally recognized expert on the Arctic region, of spying for Chinese intelligence. This development highlights the competitive relationship between the two neighboring countries, who in recent years have tended to work together against what they perceive as a common threat coming from the United States.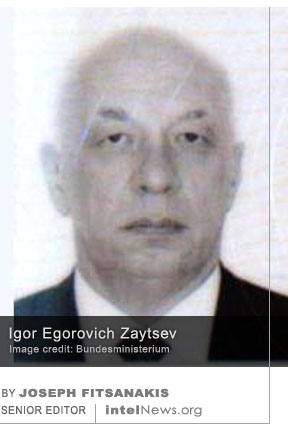 A court in Austria has found a retired Army colonel guilty of providing classified military information to Russia, following a closed-door trial. Interestingly, the alleged spy’s name has not been made public. Some Austrian media have been referring to him as “Martin M.”.
A court in Austria has found a retired Army colonel guilty of providing classified military information to Russia, following a closed-door trial. Interestingly, the alleged spy’s name has not been made public. Some Austrian media have been referring to him as “Martin M.”. Members of neo-Nazi groups in Germany attended paramilitary training camps in Russia, which were organized by a group that the United States has designated a global terrorist organization, but which the Russian government has not banned. If true, these claims add further credence to the view that Russian far-right groups are becoming increasingly central in the worldwide network of racially motivated radical organizations.
Members of neo-Nazi groups in Germany attended paramilitary training camps in Russia, which were organized by a group that the United States has designated a global terrorist organization, but which the Russian government has not banned. If true, these claims add further credence to the view that Russian far-right groups are becoming increasingly central in the worldwide network of racially motivated radical organizations. Moscow has reacted angrily to the Czech government’s decision to expel two Russian diplomats from the country, in response to allegations that the Kremlin plotted to assassinate three outspoken Czech politicians using a deadly poison. Russian officials pledged to respond in kind to Prague’s “indecent and unworthy deed”.
Moscow has reacted angrily to the Czech government’s decision to expel two Russian diplomats from the country, in response to allegations that the Kremlin plotted to assassinate three outspoken Czech politicians using a deadly poison. Russian officials pledged to respond in kind to Prague’s “indecent and unworthy deed”. The United States Defense Intelligence Agency, a Pentagon organization tasked with collecting foreign military secrets, has rejected reports that it is spying on protestors inside the country. However, it confirmed that it has set up an “internal coordination group” to respond to “requests for information” by the Department of Defense. This development follows reports that some DIA employees communicated their concerns about being asked to spy domestically to the organization’s director last week.
The United States Defense Intelligence Agency, a Pentagon organization tasked with collecting foreign military secrets, has rejected reports that it is spying on protestors inside the country. However, it confirmed that it has set up an “internal coordination group” to respond to “requests for information” by the Department of Defense. This development follows reports that some DIA employees communicated their concerns about being asked to spy domestically to the organization’s director last week. The embassy of the United States in the United Arab Emirates declined free COVID-19 testing kits for its staff, because of concerns that the private labs offering the kits had ties to China, according to a new report. The testing kits were offered by a testing facility that was set up in March in Abu Dhabi, which is the capital of the oil-rich UAE —a close American ally in the Middle East.
The embassy of the United States in the United Arab Emirates declined free COVID-19 testing kits for its staff, because of concerns that the private labs offering the kits had ties to China, according to a new report. The testing kits were offered by a testing facility that was set up in March in Abu Dhabi, which is the capital of the oil-rich UAE —a close American ally in the Middle East. In a recent video message, the new head of the Islamic State calls COVID-19 a “great torment” from God against unbelievers, and vows that “not a single day will pass without bloodshed” due to attacks by his forces. The 39-minute video is entitled “The Crusaders Will Know Who Will Win in the End”, and began to circulate on the popular messaging application Telegram last Thursday.
In a recent video message, the new head of the Islamic State calls COVID-19 a “great torment” from God against unbelievers, and vows that “not a single day will pass without bloodshed” due to attacks by his forces. The 39-minute video is entitled “The Crusaders Will Know Who Will Win in the End”, and began to circulate on the popular messaging application Telegram last Thursday. The former president of Argentina, Mauricio Macri, has been indicted as part of a widening investigation into a domestic spying program, which allegedly targeted opposition politicians, journalists and other public figures. The alleged espionage took place between 2015 and 2019, when Macri occupied the country’s highest office.
The former president of Argentina, Mauricio Macri, has been indicted as part of a widening investigation into a domestic spying program, which allegedly targeted opposition politicians, journalists and other public figures. The alleged espionage took place between 2015 and 2019, when Macri occupied the country’s highest office. India has expelled two officials at the High Commission of Pakistan in New Delhi, after they were allegedly caught with fake Indian identity papers while trying to acquire classified documents. But the Pakistani government has rejected the allegations and subsequent expulsions as “a part of persistent anti-Pakistan propaganda” from India, and said the two officials were tortured while under detention by Indian authorities.
India has expelled two officials at the High Commission of Pakistan in New Delhi, after they were allegedly caught with fake Indian identity papers while trying to acquire classified documents. But the Pakistani government has rejected the allegations and subsequent expulsions as “a part of persistent anti-Pakistan propaganda” from India, and said the two officials were tortured while under detention by Indian authorities. As the Islamic State continues to transfer its activities online due to the coronavirus pandemic, the group has published the first issue of a new cybersecurity magazine, aimed at helping its members evade surveillance. The Islamic State, known previously as the Islamic State of Iraq and Syria, has always been active online. But the COVID-19 pandemic has prompted it to
As the Islamic State continues to transfer its activities online due to the coronavirus pandemic, the group has published the first issue of a new cybersecurity magazine, aimed at helping its members evade surveillance. The Islamic State, known previously as the Islamic State of Iraq and Syria, has always been active online. But the COVID-19 pandemic has prompted it to 






Turkey arrests four members of alleged French spy ring in Istanbul
June 24, 2020 by Joseph Fitsanakis Leave a comment
The Turkish daily newspaper Sabah said on Tuesday that the leader of the French-handled spy ring is named Metin Özdemir. He is reportedly a Turkish citizen who worked in the security department of the French consulate in Istanbul. According to the paper, Özdemir admitted to Turkish police that he was sent to France where he took an eight-month-long surveillance and counter-surveillance training course. He was then sent to Georgia by France’s General Directorate for External Security (DGSE), where he gathered intelligence for his French handlers. In exchange for his services, the DGSE allegedly gave Özdemir regular cash payments and offered him a job in the French Foreign Legion.
Özdemir eventually returned to Turkey and was allegedly handled by two DGSE officials that he named as “Virginia” and “Sebastian”. He recruited three more Turkish citizens, including two utility workers, who formed a spy ring. The spy ring members were supplied by the DGSE with forged credentials, identifying them as employees of Turkey’s National Intelligence Organization (MİT). According to Sabah, the spy ring supplied the DGSE with information on 120 individuals, most of whom were members of ultra-conservative religious organizations with alleged links to the Islamic State. The spy ring also allegedly spied on the Directorate of Religious Affairs, Turkey’s state-funded religious authority. Recently, however, Özdemir reportedly fell out with his French handlers and approached Turkish authorities, who promptly arrested him and the rest of the members of his spy ring.
The Sabah report comes just days after France filed a formal complaint with NATO, alleging that one of its warships was threatened in the open seas by a Turkish Navy vessel on June 10. According to French officials, the warship Courbet attempted to approach a Turkish Navy ship named Cirkin, which was believed to be smuggling weapons to Libya. The Turkish vessel refused to identify itself to the Courbet, which was inquiring on behalf of the NATO alliance. It also flashed its radar lights at the French ship, which is usually seen as a sign of impending confrontation, while its crew members were seen wearing bullet-proof vests and standing behind the ship’s mounted weapons. Turkey has denied the French allegations, but NATO said it will launch an investigation into the incident.
► Author: Joseph Fitsanakis | Date: 24 June 2020 | Permalink
Filed under Expert news and commentary on intelligence, espionage, spies and spying Tagged with 2011 Libyan civil war, DGSE (France), espionage, France, French consulate in Istanbul, Istanbul, Metin Özdemir, News, Turkey