Files released by WikiLeaks show advanced CIA technical collection methods
March 8, 2017 4 Comments
 Thousands of documents belonging to the United States Central Intelligence Agency, which were released on Tuesday by the international anti-secrecy website WikiLeaks, are almost certainly genuine. They reveal an entire universe of technical intelligence collection methods used by the CIA to extract information from digital applications and electronic devices, ranging from flash drives to smart screen televisions. WikiLeaks named the collection Vault 7, and said that it consists of nearly 8,000 web pages and 1,000 attachments. It also said that its editors redacted hundreds of pages of computer code, in order to prevent the public release of advanced cyberweapons that are allegedly used by the CIA to sabotage electronic devices and systems.
Thousands of documents belonging to the United States Central Intelligence Agency, which were released on Tuesday by the international anti-secrecy website WikiLeaks, are almost certainly genuine. They reveal an entire universe of technical intelligence collection methods used by the CIA to extract information from digital applications and electronic devices, ranging from flash drives to smart screen televisions. WikiLeaks named the collection Vault 7, and said that it consists of nearly 8,000 web pages and 1,000 attachments. It also said that its editors redacted hundreds of pages of computer code, in order to prevent the public release of advanced cyberweapons that are allegedly used by the CIA to sabotage electronic devices and systems.
The information contained in the leaked documents is almost certainly genuine, and most likely belongs to the CIA —though many of the programs listed may be jointly run by the CIA and the National Security Agency (NSA). These programs, with names such as McNUGGET, CRUNCHYLIMESKIES, ELDERPIGGY, ANGERQUAKE and WRECKINGCREW, appear to be designed to compromise computer systems using a series of sophisticated methods that force entry or exploit built-in vulnerabilities or systems. Targets include popular communications systems like Skype and WhatsApp, smartphones produced by Google and Apple, commercial software like PDF and Microsoft Windows, and even so-called smart televisions that connect to the Internet.
The WikiLeaks revelations are most likely related to operations conducted under the auspices of the Special Collection Service (SCS), a joint CIA/NSA program that dates to the earliest days of the Cold War. The program was started by the United States Armed Forces but was eventually transferred to civilian hands and monitored by the CIA. It used advanced communications-interception facilities around the world to collect information. Over the years, the CIA collaborated with the NSA and developed many SCS projects targeting several foreign countries using technical and human means. In recent years the SCS has been primarily operated by the NSA, which oversees the program’s technical platforms.
WikiLeaks did not reveal the source of the documents. But it said that they had been “circulated [by the CIA] among former US government hackers and contractors” and that it was one of the latter that leaked them to the anti-secrecy website. A statement by WikiLeaks said that Tuesday’s release, which it codenamed “Year Zero”, was part one of several installments of documents that will be released under its Vault 7 program. The site also claimed that the information in “Year Zero” has “eclipsed the total number of pages published over the first three years of the Edward Snowden NSA leaks”. The CIA, the NSA and the White House have not commented on this development.
► Author: Joseph Fitsanakis | Date: 08 March 2017 | Permalink
 The sensational assassination of Kim Jong-nam, half-brother of North Korea’s Supreme Leader Kim Jong-un, on February 13, revealed much about the current operational mindset of Pyongyang. But it also brought to light the shady network of front companies set up by the North Korean regime to facilitate the country’s illicit financial activities around the world. This extensive network permits Pyongyang to evade international sanctions against it, and to coordinate the activities of hundreds of clandestine operatives around the world. Through these activities, the reclusive country has been able to develop its weapons of mass destruction program unabated, despite concerted efforts by the United Nations to prevent it from doing so.
The sensational assassination of Kim Jong-nam, half-brother of North Korea’s Supreme Leader Kim Jong-un, on February 13, revealed much about the current operational mindset of Pyongyang. But it also brought to light the shady network of front companies set up by the North Korean regime to facilitate the country’s illicit financial activities around the world. This extensive network permits Pyongyang to evade international sanctions against it, and to coordinate the activities of hundreds of clandestine operatives around the world. Through these activities, the reclusive country has been able to develop its weapons of mass destruction program unabated, despite concerted efforts by the United Nations to prevent it from doing so. The absurdity of American politics reached new heights over the weekend, as President Donald Trump dramatically alleged on Twitter that his predecessor, Barack Obama, wiretapped his telephones last year. Even for a highly impulsive public figure known for his sensational and often-unsubstantiated allegations, Mr. Trump’s latest claims prompted a new sense of abnormality and astonishment in Washington. If the president is unable to prove his dramatic claims, his reliability will be further-eroded, and what little is left of his relationship with the American intelligence and national-security communities will disintegrate. If his allegations are proven, they will cause a scandal of unprecedented proportions from which American political institutions —including the presidency— will find it difficult to recover.
The absurdity of American politics reached new heights over the weekend, as President Donald Trump dramatically alleged on Twitter that his predecessor, Barack Obama, wiretapped his telephones last year. Even for a highly impulsive public figure known for his sensational and often-unsubstantiated allegations, Mr. Trump’s latest claims prompted a new sense of abnormality and astonishment in Washington. If the president is unable to prove his dramatic claims, his reliability will be further-eroded, and what little is left of his relationship with the American intelligence and national-security communities will disintegrate. If his allegations are proven, they will cause a scandal of unprecedented proportions from which American political institutions —including the presidency— will find it difficult to recover. order at the highest levels of the American government, Mr. Trump’s claims cannot possibly be true. American presidents have not been legally allowed to order wiretaps since 1978, when the Foreign Intelligence Surveillance Act (FISA) was established. Prompted by the abuse of executive power revealed through the Watergate scandal, FISA forces government agencies to seek the approval of specially mandated judges before installing wiretaps. If an agency like the Federal Bureau of Investigation (FBI) wants to wiretap an individual or group suspected of acting as agents of a foreign power, it must convince one of 11 federal district judges who rotate on the FISA court that the case warrants a wiretap order. Thus, before authorizing the wiretap, a FISA judge must be convinced by examining the available evidence presented before him or her.
order at the highest levels of the American government, Mr. Trump’s claims cannot possibly be true. American presidents have not been legally allowed to order wiretaps since 1978, when the Foreign Intelligence Surveillance Act (FISA) was established. Prompted by the abuse of executive power revealed through the Watergate scandal, FISA forces government agencies to seek the approval of specially mandated judges before installing wiretaps. If an agency like the Federal Bureau of Investigation (FBI) wants to wiretap an individual or group suspected of acting as agents of a foreign power, it must convince one of 11 federal district judges who rotate on the FISA court that the case warrants a wiretap order. Thus, before authorizing the wiretap, a FISA judge must be convinced by examining the available evidence presented before him or her. Britain’s primary external-intelligence agency will revert to old-fashioned ways of recruiting employees, including the co-called “tap on the shoulder” method, according to its director. Known informally as MI6, the Secret Intelligence Service (SIS) was founded in 1908 to protect Britain’s national security by collecting intelligence from foreign sources. However, the agency has had difficulty recruiting a diverse group of people, and many still view it as a professional destination for a small wealthy elite, drawn primarily from Britain’s most prestigious universities such as Oxford and Cambridge.
Britain’s primary external-intelligence agency will revert to old-fashioned ways of recruiting employees, including the co-called “tap on the shoulder” method, according to its director. Known informally as MI6, the Secret Intelligence Service (SIS) was founded in 1908 to protect Britain’s national security by collecting intelligence from foreign sources. However, the agency has had difficulty recruiting a diverse group of people, and many still view it as a professional destination for a small wealthy elite, drawn primarily from Britain’s most prestigious universities such as Oxford and Cambridge. The Islamic State is facing imminent financial collapse, according to a new study conducted by a London-based research group in association with one of the world’s leading international accounting firms. The recently launched report is entitled
The Islamic State is facing imminent financial collapse, according to a new study conducted by a London-based research group in association with one of the world’s leading international accounting firms. The recently launched report is entitled 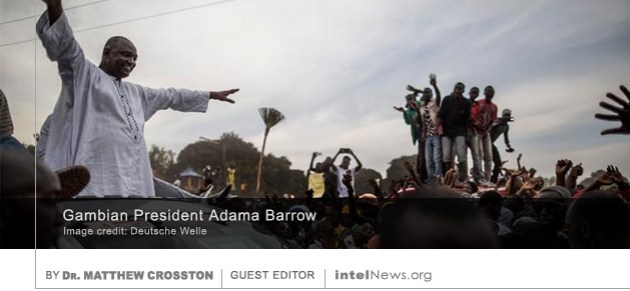 For a very long time, the field of Intelligence Studies has been dominated by analysis of the Five Eyes community, which is comprised of the United States, Great Britain, Australia, New Zealand, and Canada. In reality, that study is more often the study of intelligence in the US and the UK. While not entirely fair to characterize this as Western prejudice —access to data is better in these two countries and intelligence scholars and analysts for the most part do not fear retribution or reprisal— more voices need to come forward to consider intelligence and its role on societies beyond the Five Eyes.
For a very long time, the field of Intelligence Studies has been dominated by analysis of the Five Eyes community, which is comprised of the United States, Great Britain, Australia, New Zealand, and Canada. In reality, that study is more often the study of intelligence in the US and the UK. While not entirely fair to characterize this as Western prejudice —access to data is better in these two countries and intelligence scholars and analysts for the most part do not fear retribution or reprisal— more voices need to come forward to consider intelligence and its role on societies beyond the Five Eyes. electoral reforms back in April of 2016. The protests were geared to influencing the December 2016 presidential election, which ultimately saw the defeat of incumbent President/Strongman Yahya Jammeh to Adama Barrow. Jammeh had corruptly governed the country since rising to power as a young military officer in a bloodless military coup in 1994.
electoral reforms back in April of 2016. The protests were geared to influencing the December 2016 presidential election, which ultimately saw the defeat of incumbent President/Strongman Yahya Jammeh to Adama Barrow. Jammeh had corruptly governed the country since rising to power as a young military officer in a bloodless military coup in 1994. The military intelligence service of Sweden warned last week that there were increasing incidents of espionage perpetrated against Sweden by operatives identified “beyond doubt” as agents of foreign powers. In its
The military intelligence service of Sweden warned last week that there were increasing incidents of espionage perpetrated against Sweden by operatives identified “beyond doubt” as agents of foreign powers. In its  The White House has instructed the Central Intelligence Agency to halt military support to armed groups that are associated with the Free Syrian Army (FSA), a group opposed to Syrian President Bashar al-Assad. Some believe that the move indicates a change in American policy under United States President Donald Trump. But Syrian rebel commanders say they believe the move is temporary, and that military aid will be restored. For several years, the CIA has
The White House has instructed the Central Intelligence Agency to halt military support to armed groups that are associated with the Free Syrian Army (FSA), a group opposed to Syrian President Bashar al-Assad. Some believe that the move indicates a change in American policy under United States President Donald Trump. But Syrian rebel commanders say they believe the move is temporary, and that military aid will be restored. For several years, the CIA has  A Japanese television channel has aired
A Japanese television channel has aired  Indonesian authorities said on Sunday that they will investigate a North Korean restaurant in the country, after a Singaporean news agency claimed it was being used as a center for espionage. The announcement comes amidst heightened tensions between North Korean and its neighbors, following the
Indonesian authorities said on Sunday that they will investigate a North Korean restaurant in the country, after a Singaporean news agency claimed it was being used as a center for espionage. The announcement comes amidst heightened tensions between North Korean and its neighbors, following the  Turkish state agencies have asked the country’s diplomats stationed all over Europe to spy on Turkish expatriate communities there, in an effort to identify those opposed to the government, according to a German report. The government of Turkish President Recep Tayyip Erdoğan accuses members of the so-called Gülen movement of orchestrating a military coup in July of last year, which resulted in an armed attack on the country’s parliament and the murder of over 200 people across Turkey. The Gülen movement consists of supporters of Muslim cleric Fethullah Gülen, who runs a global network of schools, charities and businesses from his home in the United States. The government of Turkey has designated Gülen’s group a terrorist organization and claims that its members have stealthily infiltrated state institutions since the 1980s.
Turkish state agencies have asked the country’s diplomats stationed all over Europe to spy on Turkish expatriate communities there, in an effort to identify those opposed to the government, according to a German report. The government of Turkish President Recep Tayyip Erdoğan accuses members of the so-called Gülen movement of orchestrating a military coup in July of last year, which resulted in an armed attack on the country’s parliament and the murder of over 200 people across Turkey. The Gülen movement consists of supporters of Muslim cleric Fethullah Gülen, who runs a global network of schools, charities and businesses from his home in the United States. The government of Turkey has designated Gülen’s group a terrorist organization and claims that its members have stealthily infiltrated state institutions since the 1980s. In a leading article published on Wednesday, The Wall Street Journal alleged that American intelligence officials are choosing to withhold sensitive intelligence from President Donald Trump, fearing that it might be compromised. The WSJ, America’s leading newspaper by circulation, which is highly influential in conservative circles,
In a leading article published on Wednesday, The Wall Street Journal alleged that American intelligence officials are choosing to withhold sensitive intelligence from President Donald Trump, fearing that it might be compromised. The WSJ, America’s leading newspaper by circulation, which is highly influential in conservative circles, 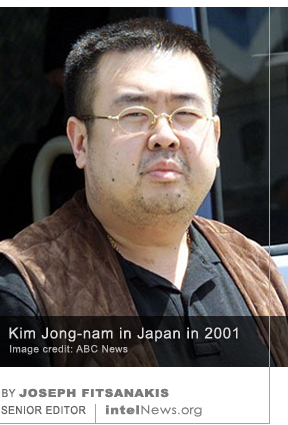 Two women have been arrested in the past 48 hours in connection with the assassination of Kim Jong-nam, half-brother of North Korea’s supreme leader, who died in Malaysia on Monday. Kim, the grandson of North Korea’s founder Kim Il-Sung, died after two women approached him at the Kuala Lumpur International Airport and splashed his face with liquid poison. Some reports suggest that he was injected with a poisoned needle.
Two women have been arrested in the past 48 hours in connection with the assassination of Kim Jong-nam, half-brother of North Korea’s supreme leader, who died in Malaysia on Monday. Kim, the grandson of North Korea’s founder Kim Il-Sung, died after two women approached him at the Kuala Lumpur International Airport and splashed his face with liquid poison. Some reports suggest that he was injected with a poisoned needle.  The half-brother of North Korean Supreme Leader Kim Jong-un has been killed in an audacious attack in Malaysia, reportedly by two female assassins who used a poisonous substance to murder him. Kim Jong-nam, was the eldest son of Kim Jong-il, and grandson of Kim Il-Sung, who founded the Democratic People’s Republic of Korea in 1948. However, he left the country in 2007, reportedly after it became clear that his younger half-brother, Kim Jong-un, was the regime’s preferred successor to his father, Kim Jong-il.
The half-brother of North Korean Supreme Leader Kim Jong-un has been killed in an audacious attack in Malaysia, reportedly by two female assassins who used a poisonous substance to murder him. Kim Jong-nam, was the eldest son of Kim Jong-il, and grandson of Kim Il-Sung, who founded the Democratic People’s Republic of Korea in 1948. However, he left the country in 2007, reportedly after it became clear that his younger half-brother, Kim Jong-un, was the regime’s preferred successor to his father, Kim Jong-il.






FBI launches criminal investigation into WikiLeaks’ CIA disclosures
March 9, 2017 by Joseph Fitsanakis 1 Comment
On Wednesday, former director of the CIA Michael Hayden told the BBC that the disclosure appeared “incredibly damaging”, because it revealed some of the methods that the CIA uses to acquire information. But some cybersecurity experts said that the techniques contained in the leaked documents did not appear to be uniquely advanced, and most focused on exploiting technical vulnerabilities that were generally known. Still, The New York Times reported on Wednesday that the CIA had begun to assess the damage caused by the release. The agency was also trying to contain the extent of the damage, and had even “halt[ed] work on some projects”, said The Times. Officials from the CIA are reportedly in communication with the Federal Bureau of Investigation, which on Wednesday launched a criminal investigation into the “Vault 7” release.
The main purpose of the FBI investigation is to find out how WikiLeaks acquired the files. The website said that the documents were leaked by a CIA contractor, which would imply that they were accessed from a server outside the CIA’s computer network. However, federal investigators are not excluding the possibility that the leaker of the information may be a full-time CIA employee. Reports suggest that the FBI is preparing to conduct hundreds, and possibly thousands, of interviews with individuals who are believed to have had access to the documents that were released by WikiLeaks. Meanwhile, neither the FBI nor the CIA have commented on the authenticity of the information contained in “Vault 7”. WikiLeaks said that Tuesday’s release, which it codenamed “Year Zero”, was the first part of several installments of documents that will be released under its Vault 7 program.
► Author: Joseph Fitsanakis | Date: 09 March 2017 | Permalink
Filed under Expert news and commentary on intelligence, espionage, spies and spying Tagged with CIA, computer hacking, News, NSA, NSA Special Collection Service, United States, Wikileaks