Russia targeted by unprecedented wave of cyber-attacks, experts say
May 3, 2022 1 Comment
 RUSSIAN STATE COMPANIES, BUSINESSES and individuals are being targeted in an unprecedented wave of attacks by digital assailants, according to observers, who say they are surprised by its ferocity. Since February of this year, hackers have accessed the personal financial data of pro-Kremlin oligarchs, stolen millions of internal emails stored on Russian government severs, and defaced high-profile websites across the nation. The Washington Post, which summarized the wave of attacks last Sunday, said they are being waged by hacker collectives, as well as common criminals. The paper claimed that the assailants are not connected to foreign governments.
RUSSIAN STATE COMPANIES, BUSINESSES and individuals are being targeted in an unprecedented wave of attacks by digital assailants, according to observers, who say they are surprised by its ferocity. Since February of this year, hackers have accessed the personal financial data of pro-Kremlin oligarchs, stolen millions of internal emails stored on Russian government severs, and defaced high-profile websites across the nation. The Washington Post, which summarized the wave of attacks last Sunday, said they are being waged by hacker collectives, as well as common criminals. The paper claimed that the assailants are not connected to foreign governments.
According to observers, Russia currently tops the global list of targeted attacks by hackers for the first time since records began. Major targets include Russia’s media regulator, the Federal Service for Supervision of Communications, Information Technology and Mass Media, which anti-government activists blame for implementing Soviet-style censorship. Hackers have also attacked Russia’s state-owned broadcaster, known as VGTRK, as well the Russian intelligence and defense establishments. Tens of thousands of emails exchanged by senior VGTRK officials since 2013 were recently stolen and leaked in a massive data dump. Additionally, lengthy lists containing the names of alleged Russian intelligence officers, as well as of soldiers, have been leaked online by unknown hackers.
The attacks are led by political hacker collectives, including Network Battalion 65 (NB65), which announced its existence on Twitter just hours after Russian troops began to march toward Kyiv. The group is believed to have links to the international hacktivist collective Anonymous, and claims to have no ties to governments. Another hacker collective that is behind the attacks on Russia is a group calling itself AgainstTheWest. Despite its name, it is led by a group of pro-Western, “English-speaking hackers […] with intelligence backgrounds”, according to The Post. Attacks are also being perpetrated by smaller groups of hackers, some of them based in Ukraine, and by criminal groups, whose members are motivated by profit and are attacking Russian state targets at a time when the Kremlin appears vulnerable.
According to the paper, the Ukrainian government is not directly involved in these cyber-attacks. However, it has repeatedly endorsed attacks by hackers aimed at weakening the Russian state. Back in February, Ukraine’s Deputy Prime Minister and Digital Transformation Minister issued an open call for the formation of a “volunteer cyber army” to fight for Ukraine. As intelNews reported at the time, the Ukrainian government claimed that nearly 200,000 people had shown interest in joining the initiative. However, little has been mentioned since. The government of Ukraine maintains an “IT Army” channel on Telegram, where it frequently suggests Russian targets that pro-Ukrainian hackers should attack. However, any evidence of links between it and the wave of cyber-attacks that Russia has been experiencing remains speculative.
► Author: Ian Allen | Date: 03 May 2022 | Permalink
 ISRAEL’S MOSSAD INTELLIGENCE AGENCY allegedly foiled a plot by Iranian intelligence to send assassins abroad and kill an Israeli diplomat, an American military official and a French reporter, according to reports. The information about the alleged plot first surfaced late last week in the Iran International News Channel, a British-based Iranian news agency, which is opposed to the government in Tehran. The news agency claimed that the plot had been organized by the Quds Force, the paramilitary wing of the Islamic Revolutionary Guards Corps.
ISRAEL’S MOSSAD INTELLIGENCE AGENCY allegedly foiled a plot by Iranian intelligence to send assassins abroad and kill an Israeli diplomat, an American military official and a French reporter, according to reports. The information about the alleged plot first surfaced late last week in the Iran International News Channel, a British-based Iranian news agency, which is opposed to the government in Tehran. The news agency claimed that the plot had been organized by the Quds Force, the paramilitary wing of the Islamic Revolutionary Guards Corps. SOUTH KOREAN AUTHORITIES HAVE busted an alleed spy ring run by a North Korean handler, who remains at large. Two men have been arrested so far in connection with the ring. One of them, identified only as “Lee”, is
SOUTH KOREAN AUTHORITIES HAVE busted an alleed spy ring run by a North Korean handler, who remains at large. Two men have been arrested so far in connection with the ring. One of them, identified only as “Lee”, is  THE RUSSIAN FEDERATION HAS reportedly ordered 175,000 new diplomatic passports to be printed, prompting speculation about their possible use at a time when Western sanctions are affecting Russia’s governing elite. Diplomatic passports are travel documents that are issued to accredited diplomats and government officials, such as foreign ministry envoys and others. Pursuant to the Vienna Convention of Diplomatic Relations, holders of diplomatic passports enjoy diplomatic immunity and are typically subjected to very limited inspections by security personnel when crossing international borders.
THE RUSSIAN FEDERATION HAS reportedly ordered 175,000 new diplomatic passports to be printed, prompting speculation about their possible use at a time when Western sanctions are affecting Russia’s governing elite. Diplomatic passports are travel documents that are issued to accredited diplomats and government officials, such as foreign ministry envoys and others. Pursuant to the Vienna Convention of Diplomatic Relations, holders of diplomatic passports enjoy diplomatic immunity and are typically subjected to very limited inspections by security personnel when crossing international borders. AUSTRALIAN INTELLIGENCE HAD A role in the mysterious disclosure of a secret memorandum about a controversial defense pact between China and the Solomon Islands, which is causing consternation in the West. Western leaders claim that the pact will turn the tiny Melanesian nation into a logistical hub for Chinese warships in a strategic region of the Pacific Ocean. The pact also stipulates a training role for Chinese police and military personnel, who are called to “assist […] in maintaining social order” in the island nation.
AUSTRALIAN INTELLIGENCE HAD A role in the mysterious disclosure of a secret memorandum about a controversial defense pact between China and the Solomon Islands, which is causing consternation in the West. Western leaders claim that the pact will turn the tiny Melanesian nation into a logistical hub for Chinese warships in a strategic region of the Pacific Ocean. The pact also stipulates a training role for Chinese police and military personnel, who are called to “assist […] in maintaining social order” in the island nation. TELEPHONE SYSTEMS BELONGING TO the British government were compromised by the Pegasus surveillance software, according to a Canadian research group. The allegation was made on Monday in an investigative
TELEPHONE SYSTEMS BELONGING TO the British government were compromised by the Pegasus surveillance software, according to a Canadian research group. The allegation was made on Monday in an investigative  CHINESE STATE-OWNED MEDIA has stepped up warnings of an alleged Western espionage offensive, to mark China’s annual “national security education day”, a new initiative promoted by the Chinese Communist Party (CPC). The decision to designate April 15 “national security education day” was adopted by the CPC in 2015, during its 12th National People’s Congress. Since then, the Chinese government has promoted the day as an effort to create a “positive atmosphere of national security” across the nation.
CHINESE STATE-OWNED MEDIA has stepped up warnings of an alleged Western espionage offensive, to mark China’s annual “national security education day”, a new initiative promoted by the Chinese Communist Party (CPC). The decision to designate April 15 “national security education day” was adopted by the CPC in 2015, during its 12th National People’s Congress. Since then, the Chinese government has promoted the day as an effort to create a “positive atmosphere of national security” across the nation. More than 150 officers have been purged form the ranks of Russia’s Federal Security Service (FSB), as President Vladimir Putin is placing blame on his intelligence agencies for the setbacks experienced during the invasion of Ukraine. This assessment was communicated to the London-based Times newspaper by British intelligence sources, who added that many of those purged have been dismissed from the service, while others remain under house arrest. A few —among them senior FSB officials— are in prison. The FSB is tasked with domestic security and counterintelligence operations, which were carried out by the KGB during the Cold War.
More than 150 officers have been purged form the ranks of Russia’s Federal Security Service (FSB), as President Vladimir Putin is placing blame on his intelligence agencies for the setbacks experienced during the invasion of Ukraine. This assessment was communicated to the London-based Times newspaper by British intelligence sources, who added that many of those purged have been dismissed from the service, while others remain under house arrest. A few —among them senior FSB officials— are in prison. The FSB is tasked with domestic security and counterintelligence operations, which were carried out by the KGB during the Cold War. AN AMERICAN COMPUTER PROGRAMMER has been jailed for 63 months for providing “highly technical information” to North Korea, which related to cryptocurrency systems, according to United States officials. The programmer, Virgil Griffith, 39, also known as “Romanpoet”, became widely known in the early 2000s, when he began describing himself as a “disruptive technologist”. He later consulted with the Federal Bureau of Investigation and other law enforcement agencies in the area of the dark web and cryptocurrencies.
AN AMERICAN COMPUTER PROGRAMMER has been jailed for 63 months for providing “highly technical information” to North Korea, which related to cryptocurrency systems, according to United States officials. The programmer, Virgil Griffith, 39, also known as “Romanpoet”, became widely known in the early 2000s, when he began describing himself as a “disruptive technologist”. He later consulted with the Federal Bureau of Investigation and other law enforcement agencies in the area of the dark web and cryptocurrencies. A LEAKED PLAN FOR a security alliance between China and the small Melanesian nation of the Solomon Islands has sparked concerns about a large-scale military buildup by regional powers in the South Pacific. The draft agreement, which was leaked online last week, appears to turn the Solomon Islands into a logistical hub for Chinese warships. It also stipulates a training role for Chinese police and military personnel, who are called to “assist […] in maintaining social order” in the island nation.
A LEAKED PLAN FOR a security alliance between China and the small Melanesian nation of the Solomon Islands has sparked concerns about a large-scale military buildup by regional powers in the South Pacific. The draft agreement, which was leaked online last week, appears to turn the Solomon Islands into a logistical hub for Chinese warships. It also stipulates a training role for Chinese police and military personnel, who are called to “assist […] in maintaining social order” in the island nation. A BRITISH CITIZEN, WHO worked as a security guard at the British embassy in Berlin, has been charged with spying for the Russian intelligence services. Authorities in the United Kingdom announced on Wednesday that David Ballantyne Smith, 57, who lives in Potsdam, Germany, has been charged on nine different offenses under the 1911 Official Secrets Act.
A BRITISH CITIZEN, WHO worked as a security guard at the British embassy in Berlin, has been charged with spying for the Russian intelligence services. Authorities in the United Kingdom announced on Wednesday that David Ballantyne Smith, 57, who lives in Potsdam, Germany, has been charged on nine different offenses under the 1911 Official Secrets Act. FOUR RUSSIAN DIPLOMATS, WHO Ireland claims are undercover intelligence officers, met with Irish paramilitaries as part of a wider plan to “stoke political unrest” in Britain and Ireland, according to a new report. In a press conference held in Dublin last week, Irish Taoiseach (Prime Minister) Micheál Martin
FOUR RUSSIAN DIPLOMATS, WHO Ireland claims are undercover intelligence officers, met with Irish paramilitaries as part of a wider plan to “stoke political unrest” in Britain and Ireland, according to a new report. In a press conference held in Dublin last week, Irish Taoiseach (Prime Minister) Micheál Martin  A WEEK AFTER POLAND
A WEEK AFTER POLAND 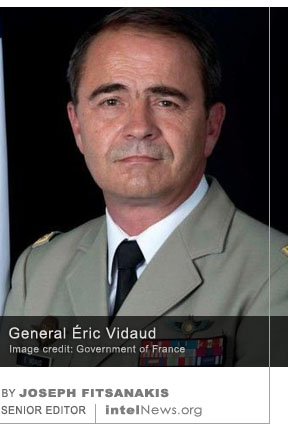 THE DIRECTOR OF FRANCE’S military intelligence agency has been asked to resign, allegedly because of his agency’s failure to anticipate the Russian invasion of Ukraine. General Éric Vidaud is a career military officer, who rose through the ranks to command the 1st Marine Infantry Parachute Regiment, one of the three units in the French Army Special Forces Command. In 2018, he was placed at the helm of the Special Operations Command, which oversees the joint activities of special forces units from all of France’s military branches. In August of last year, Vidaud assumed command of the Directorate of Military Intelligence (DRM), which operates under France’s Armed Forces Ministry.
THE DIRECTOR OF FRANCE’S military intelligence agency has been asked to resign, allegedly because of his agency’s failure to anticipate the Russian invasion of Ukraine. General Éric Vidaud is a career military officer, who rose through the ranks to command the 1st Marine Infantry Parachute Regiment, one of the three units in the French Army Special Forces Command. In 2018, he was placed at the helm of the Special Operations Command, which oversees the joint activities of special forces units from all of France’s military branches. In August of last year, Vidaud assumed command of the Directorate of Military Intelligence (DRM), which operates under France’s Armed Forces Ministry.






Newly discovered cyber-espionage group spies for money using state-actor methods
May 4, 2022 by Joseph Fitsanakis 1 Comment
Given its targets, as well as the information it goes after, there is little doubt that UNC3524 is interested in financial gain. However, its operational profile differs markedly from those of other financially oriented hacker groups, according to Mandiant. Its sophisticated approach to espionage demonstrates aspects that are typically associated with government-sponsored intelligence operations. Notably, UNC3524 operatives take their time to get to know their targets, and are not in a hurry to exploit the online environments they penetrate. Mandiant reported that UNC3524 attacks can take up to 18 months to conclude. In contrast, the average financially-motivated cyber-espionage attack rarely lasts longer than three weeks.
Additionally, UNC3524 operatives make a point of maintaining an extremely stealthy and low-key online profile, and have even developed a series of novel exploitation techniques, which Mandiant has termed “QuietExit”. The latter appear to focus on exploiting Internet of Things (IoT) devices that are typically found in corporate settings, but are not protected by traditional anti-virus systems. Once they penetrate the digital environment of their target, UNC3524 operatives meticulously build sophisticated back-doors into the system, and are known to return sometimes within hours after they are detected and repelled.
Interestingly, UNC3524 operatives do not waste time on low-level employees of targeted corporations. Once inside, they go straight for executive-level targets, including those in corporate strategy and development, mergers and acquisitions, and even information security. Mandiant says a few other actors, notably Russian-linked groups like Cozy Bear, Fancy Bear, APT28 or APT29, are also known to operate with such high-level targets in mind. However, there is little other operational overlap between them and UNC3524, the blog post claims.
► Author: Joseph Fitsanakis | Date: 04 May 2022 | Permalink
Filed under Expert news and commentary on intelligence, espionage, spies and spying Tagged with computer hacking, cyber security, cyberespionage, Mandiant, News, UNC3524