Holland expels two Iranian diplomats, but stays silent on reasons
July 9, 2018 Leave a comment
 Holland has expelled two Iranian diplomats without saying why, leading to speculation that the expulsions may be related to the arrests of members of an alleged Iranian sleeper cell in Belgium, Germany and France last week. On Friday, a spokesperson from Holland’s General Intelligence and Security Service (AIVD) told reporters that “two persons accredited to the Iranian embassy” in the Hague “were expelled from the Netherlands on June 7”. The spokesperson continued saying that, although the AIVD was able to confirm that the two unnamed persons had been expelled from the country, they would “not provide any further information”. When journalists contacted Holland’s Ministry of Foreign Affairs, they were told that there would be no comment on the matter from the Dutch government.
Holland has expelled two Iranian diplomats without saying why, leading to speculation that the expulsions may be related to the arrests of members of an alleged Iranian sleeper cell in Belgium, Germany and France last week. On Friday, a spokesperson from Holland’s General Intelligence and Security Service (AIVD) told reporters that “two persons accredited to the Iranian embassy” in the Hague “were expelled from the Netherlands on June 7”. The spokesperson continued saying that, although the AIVD was able to confirm that the two unnamed persons had been expelled from the country, they would “not provide any further information”. When journalists contacted Holland’s Ministry of Foreign Affairs, they were told that there would be no comment on the matter from the Dutch government.
Late on Friday, the Reuters news agency cited an unnamed “European government official and a Western intelligence source” who said that the two Iranian embassy personnel were expelled from Holland “up to two months ago”. But Holland’s state-owned Dutch Broadcast Foundation (NOS) reported that the expulsions took place on June 7. No further information appears to be publicly available. However, assuming that the expulsions took place last week, and not two months ago, they appear to have coincided with the arrests of members of an alleged Iranian sleeper cell on June 30 and July 1. As intelNews reported last week, the arrests began on June 30, when members of Belgium’s Special Forces Group arrested a married Belgian couple of Iranian descent in Brussels. The couple were found to be carrying explosives and a detonator. On the following day, July 1, German police arrested an Iranian diplomat stationed in Iran’s embassy in Vienna, Austria. On the same day, a fourth person, who has not been named, was arrested by authorities in France, reportedly in connection with the three other arrests.
All four individuals appear to have been charged with a foiled plot to bomb the annual conference of the National Council of Resistance of Iran (NCRI) that took place on June 30 in Paris. The NCRI is led by Mujahedin-e Khalq (MEK), a Marxist militant group that has roots in radical Islam and Marxism. Until a few years ago, the MEK was designated as a terrorist group by the European Union and the United States, but has since been reinstated in both Brussels and Washington. There is also speculation that last week’s expulsions in Holland may be related to the assassinations of dissident Iranian expatriates in Holland in 2015 and 2017, which have been blamed on the government in Tehran.
On Saturday, the Iranian Ministry of Foreign Affairs summoned the Dutch ambassador to protest against the expulsions of its diplomats, while a ministry spokesperson warned that “the Islamic Republic reserves the right to retaliate”. Reuters quoted an unnamed “senior Iranian official” who said that “all these arrests and expulsions are part of our enemies’ attempts to harm efforts to salvage the nuclear deal”, a reference to the Joint Comprehensive Plan of Action.
► Author: Joseph Fitsanakis | Date: 09 July 2018 | Research credit: M.K. | Permalink
 An Iranian diplomat and members of what authorities described as an “Iranian sleeper cell” were arrested this week in Belgium, Germany and France, as they were allegedly planning to a bomb a high-level meeting in Paris. The arrests came after a complex investigation by several European intelligence agencies and were announced by Belgium’s Minister of the Interior, Jan Jambon.
An Iranian diplomat and members of what authorities described as an “Iranian sleeper cell” were arrested this week in Belgium, Germany and France, as they were allegedly planning to a bomb a high-level meeting in Paris. The arrests came after a complex investigation by several European intelligence agencies and were announced by Belgium’s Minister of the Interior, Jan Jambon. A United States federal judge ruled on Monday that a tweet by President Donald Trump did not inadvertently disclose a top-secret program by the Central Intelligence Agency to aid rebel groups in Syria. The lawsuit, brought by The New York Times, centered on news reports published in 2017 by
A United States federal judge ruled on Monday that a tweet by President Donald Trump did not inadvertently disclose a top-secret program by the Central Intelligence Agency to aid rebel groups in Syria. The lawsuit, brought by The New York Times, centered on news reports published in 2017 by  The daughter of Heinrich Himmler, who was second in command in the German Nazi Party until the end of World War II, worked for West German intelligence in the 1960s, it has been confirmed. Gudrun Burwitz was born Gudrun Himmler in 1929. During the reign of Adolf Hitler, her father, Heinrich Himmler, commanded the feared Schutzstaffel, known more commonly as the SS. Under his command, the SS played a central part in administering the Holocaust, and carried out a systematic campaign of extermination of millions of civilians in Nazi-occupied Europe. But the Nazi regime collapsed under the weight of the Allied military advance, and on May 20, 1945, Himmler was captured alive by Soviet troops. Shortly thereafter he was transferred to a British-administered prison, where, just days later, he committed suicide with a cyanide capsule that he had with him. Gudrun, who by that time was nearly 16 years old, managed to escape to Italy with her mother, where she was captured by American forces. She testified in the Nuremberg Trials and was eventually released in 1948. She settled with her mother in northern West Germany and lived away from the limelight of publicity until her death on May 24 of this year, aged 88.
The daughter of Heinrich Himmler, who was second in command in the German Nazi Party until the end of World War II, worked for West German intelligence in the 1960s, it has been confirmed. Gudrun Burwitz was born Gudrun Himmler in 1929. During the reign of Adolf Hitler, her father, Heinrich Himmler, commanded the feared Schutzstaffel, known more commonly as the SS. Under his command, the SS played a central part in administering the Holocaust, and carried out a systematic campaign of extermination of millions of civilians in Nazi-occupied Europe. But the Nazi regime collapsed under the weight of the Allied military advance, and on May 20, 1945, Himmler was captured alive by Soviet troops. Shortly thereafter he was transferred to a British-administered prison, where, just days later, he committed suicide with a cyanide capsule that he had with him. Gudrun, who by that time was nearly 16 years old, managed to escape to Italy with her mother, where she was captured by American forces. She testified in the Nuremberg Trials and was eventually released in 1948. She settled with her mother in northern West Germany and lived away from the limelight of publicity until her death on May 24 of this year, aged 88. The head of Austria’s counterintelligence agency has said that Brussels has now replaced Vienna as Europe’s spy capital. For nearly a decade, this blog has published expert commentary that points to the Austrian capital being the world’s busiest spy den. In 2009, German broadsheet Die Welt
The head of Austria’s counterintelligence agency has said that Brussels has now replaced Vienna as Europe’s spy capital. For nearly a decade, this blog has published expert commentary that points to the Austrian capital being the world’s busiest spy den. In 2009, German broadsheet Die Welt  Dozens of Dutch security officers, legal experts, diplomats and other civil servants were systematically spied on by Ukrainian and Russian intelligence services while probing the aftermath of the MH17 disaster, according to a report on Dutch television. Malaysia Airlines Flight 17, a scheduled passenger flight from Amsterdam to Kuala Lumpur, was
Dozens of Dutch security officers, legal experts, diplomats and other civil servants were systematically spied on by Ukrainian and Russian intelligence services while probing the aftermath of the MH17 disaster, according to a report on Dutch television. Malaysia Airlines Flight 17, a scheduled passenger flight from Amsterdam to Kuala Lumpur, was  The Norwegian National Security Authority (NSM) has warned the country’s information technology firms to prioritize national security over cutting costs when outsourcing their operations abroad. The warning follows what has come to be known as the “Broadnet affair”, which, according to the Norwegian government, highlighted the dangers of extreme cost-cutting measures by Norway’s heavily privatized IT industry. The incident is named after Broadnet, Norway’s leading supplier of fiber-optic communications to the country’s industry and state sectors. Among Broadnet’s customers is Nødnett, an extensive digital network used by agencies and organizations that engage in rescue and emergency operations, including police and fire departments, as well as medical response agencies. Although 60% of the Nødnett network is owned by the Norwegian government, Broadnet is a member of the Nødnett consortium, and is thus supervised by Norway’s Ministry of Transport and Communications.
The Norwegian National Security Authority (NSM) has warned the country’s information technology firms to prioritize national security over cutting costs when outsourcing their operations abroad. The warning follows what has come to be known as the “Broadnet affair”, which, according to the Norwegian government, highlighted the dangers of extreme cost-cutting measures by Norway’s heavily privatized IT industry. The incident is named after Broadnet, Norway’s leading supplier of fiber-optic communications to the country’s industry and state sectors. Among Broadnet’s customers is Nødnett, an extensive digital network used by agencies and organizations that engage in rescue and emergency operations, including police and fire departments, as well as medical response agencies. Although 60% of the Nødnett network is owned by the Norwegian government, Broadnet is a member of the Nødnett consortium, and is thus supervised by Norway’s Ministry of Transport and Communications.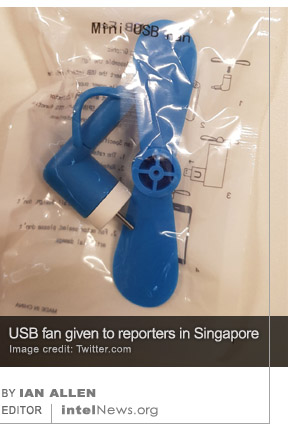 Singaporean officials have dismissed reports that a promotional item given away for free during the June 12 summit between the leaders of the United States and North Korea contained an espionage device. Over 2500 reporters from nearly every country covered the meeting between US President Donald Trump and North Korean Supreme Leader Kim Jong-un. Upon arriving in Singapore’s Sentosa Island, where the summit took place, journalists were given a free promotional packet that included novelty items such as pens, notepads, a water bottle, and a USB fan. The USB fan consisted of blades connected to a miniature electric motor, which was in turn connected to a USB cable. The cable allowed the device to be powered by a computer or other electronic device with a built-in USB port.
Singaporean officials have dismissed reports that a promotional item given away for free during the June 12 summit between the leaders of the United States and North Korea contained an espionage device. Over 2500 reporters from nearly every country covered the meeting between US President Donald Trump and North Korean Supreme Leader Kim Jong-un. Upon arriving in Singapore’s Sentosa Island, where the summit took place, journalists were given a free promotional packet that included novelty items such as pens, notepads, a water bottle, and a USB fan. The USB fan consisted of blades connected to a miniature electric motor, which was in turn connected to a USB cable. The cable allowed the device to be powered by a computer or other electronic device with a built-in USB port. One of China’s most senior shipbuilding executives, who has not been seen in public for nearly two weeks, has been charged with giving secrets about China’s aircraft carriers to the United States. Sun Bo, 57, is general manager of the China Shipbuilding Industry Corporation (CSIC), China’s largest state-owned maritime manufacturer, which leads nearly every major shipbuilding project of the Chinese navy. Most notably, Sun headed the decade-long retrofitting of the Liaoning, a Soviet-built aircraft carrier that was commissioned to the Chinese Navy’s Surface Force after the collapse of the Soviet Union.
One of China’s most senior shipbuilding executives, who has not been seen in public for nearly two weeks, has been charged with giving secrets about China’s aircraft carriers to the United States. Sun Bo, 57, is general manager of the China Shipbuilding Industry Corporation (CSIC), China’s largest state-owned maritime manufacturer, which leads nearly every major shipbuilding project of the Chinese navy. Most notably, Sun headed the decade-long retrofitting of the Liaoning, a Soviet-built aircraft carrier that was commissioned to the Chinese Navy’s Surface Force after the collapse of the Soviet Union. The head of Germany’s domestic security agency has publicly blamed the Russian government for a large-scale cyberattack that has targeted German energy providers. The comments follow a June 13 announcement on the subject by Germany’s Federal Office for Information Security (BSI), which is charged with securing the German government’s electronic communications. According to the BSI, a widespread and systematic attack against Germany’s energy networks has been taking place for at least a year now. The attack, which the BSI codenamed BERSERK BEAR, consists of various efforts by hackers to compromise computer networks used by German companies that provide electricity and natural gas to consumers around the country.
The head of Germany’s domestic security agency has publicly blamed the Russian government for a large-scale cyberattack that has targeted German energy providers. The comments follow a June 13 announcement on the subject by Germany’s Federal Office for Information Security (BSI), which is charged with securing the German government’s electronic communications. According to the BSI, a widespread and systematic attack against Germany’s energy networks has been taking place for at least a year now. The attack, which the BSI codenamed BERSERK BEAR, consists of various efforts by hackers to compromise computer networks used by German companies that provide electricity and natural gas to consumers around the country.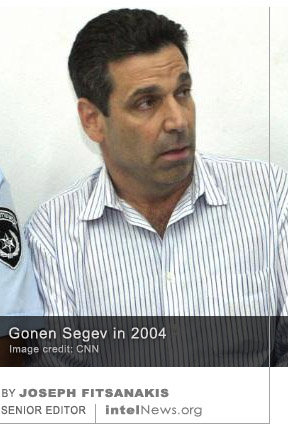 Israel has charged Gonen Segev, who served as the Jewish state’s Minister of Energy and Infrastructure, with spying for its archenemy, Iran. Segev, 62, was reportedly detained last month during a trip to Equatorial Guinea following a request by Israeli officials. He was then extradited to Israel and arrested as soon as he arrived in Tel Aviv last month, according to a statement by the Shin Bet, Israel’s domestic security service. On Monday it emerged that Israeli authorities had imposed a gag order on the case, forbidding Israeli media from reporting any information about it. The order appears to have now been lifted.
Israel has charged Gonen Segev, who served as the Jewish state’s Minister of Energy and Infrastructure, with spying for its archenemy, Iran. Segev, 62, was reportedly detained last month during a trip to Equatorial Guinea following a request by Israeli officials. He was then extradited to Israel and arrested as soon as he arrived in Tel Aviv last month, according to a statement by the Shin Bet, Israel’s domestic security service. On Monday it emerged that Israeli authorities had imposed a gag order on the case, forbidding Israeli media from reporting any information about it. The order appears to have now been lifted. German authorities have charged a Tunisian citizen with building a biological weapon, after finding significant quantities of the highly toxic substance ricin in his apartment. The 29-year-old man is referred to in public reports only as “Sief Allah H.”, in compliance with German law that forbids the naming of suspects until they are found guilty in court. German officials said last Thursday that the man remains in custody and has been charged with violating Germany’s War Weapons Control Act (known as Kriegswaffenkontrollgesetz) and “preparing a serious act of violence against the state”.
German authorities have charged a Tunisian citizen with building a biological weapon, after finding significant quantities of the highly toxic substance ricin in his apartment. The 29-year-old man is referred to in public reports only as “Sief Allah H.”, in compliance with German law that forbids the naming of suspects until they are found guilty in court. German officials said last Thursday that the man remains in custody and has been charged with violating Germany’s War Weapons Control Act (known as Kriegswaffenkontrollgesetz) and “preparing a serious act of violence against the state”. Belgium will investigate whether Spanish intelligence spied on Carles Puigdemont, the separatist Catalan leader who escaped to Brussels after launching an unsuccessful independence bid last year. Puigdemont, 56, served as president of the Spanish region of Catalonia from January 2016 until October 2017. He was forcibly removed from office by the Spanish government, after he led the government of Catalonia in a unilateral declaration of independence from Spain. As soon as the Catalan Parliament declared that the region was independent, Madrid dissolved it, imposed direct rule on the country’s easternmost province, and declared fresh elections.
Belgium will investigate whether Spanish intelligence spied on Carles Puigdemont, the separatist Catalan leader who escaped to Brussels after launching an unsuccessful independence bid last year. Puigdemont, 56, served as president of the Spanish region of Catalonia from January 2016 until October 2017. He was forcibly removed from office by the Spanish government, after he led the government of Catalonia in a unilateral declaration of independence from Spain. As soon as the Catalan Parliament declared that the region was independent, Madrid dissolved it, imposed direct rule on the country’s easternmost province, and declared fresh elections. The United States has for the first time imposed economic sanctions on a number of Russian companies, which it says helped the Kremlin spy on targets in North America and Western Europe. On Monday, the US Department of the Treasury said it would apply severe economic restrictions on a number of Russian firms that work closely with the Kremlin. One of the companies was
The United States has for the first time imposed economic sanctions on a number of Russian companies, which it says helped the Kremlin spy on targets in North America and Western Europe. On Monday, the US Department of the Treasury said it would apply severe economic restrictions on a number of Russian firms that work closely with the Kremlin. One of the companies was 






North Korea asked Israel for $1 billion to stop giving missile technology to Iran
July 10, 2018 by Joseph Fitsanakis Leave a comment
Now Thae has written a book about his experiences as a North Korean diplomat from a family that is close to the country’s ruling Kim dynasty. In his memoir, Thae claims that he acted as a translator during a series of meetings between Son Mu Sin and Gideon Ben Ami, respectively North Korea’s and Israel’s ambassadors to Sweden. The alleged meetings took place in secret in the winter of 1999 in Stockholm, says Thae. During the first meeting, Son allegedly told Ben Ami that Pyongyang had a series of agreements to sell ballistic missile technology and know-how to Israel’s adversaries, such as Syria, Pakistan and Iran. However, the North Korean government would be willing to scrap the agreements in exchange for $1 billion in cash from Israel, said Son. Ben Ami reportedly told his North Korean counterpart that he would pass along his offer to the Israeli government. Three days later, says Thae, the two men held another secret meeting, during which the North Korean ambassador was told that Israel was not willing to pay Pyongyang $1 billion in cash. However, it could offer humanitarian aid of equal value. But according to Thae the North Koreans refused and “the talks ended without an agreement”.
It is believed that North Korea then went ahead and supplied both Syria and Iran with missile and nuclear technology. On Sunday, The Wall Street Journal reported that it contacted the government of Israel with several questions stemming from Thae’s account of the alleged diplomatic exchange of 1999. However, it received no response. The paper also tried to elicit responses from Ben Ami and Son, but had no success. According to The Journal, Ben Ami said during a television interview last week that he held three meetings with a group of North Korean officials in 1999. But he did not name the diplomats, nor did he discuss the subject of his conversations with them.
► Author: Joseph Fitsanakis | Date: 10 July 2018 | Permalink
Filed under Expert news and commentary on intelligence, espionage, spies and spying Tagged with Gideon Ben Ami, Israel, News, North Korea, North Korean nuclear program, Son Mu Sin, Thae Yong Ho