Militaries around the world scramble to contain impact of COVID-19
March 11, 2020 1 Comment
 Military forces around the world are scrambling to contain the impact of COVID-19 on military readiness, as the virus continues to infect troops and commanders at an alarming rate. On Tuesday, the Polish government announced that General Jaroslaw Mika, who serves as general commander of Branches of the Armed Forces, had tested positive for the coronavirus. General Mika is believed to have contracted the virus during a military conference that took place in the German city of Wiesbaden, where North Atlantic Treaty Organization commanders gathered to plan an American-led military exercise.
Military forces around the world are scrambling to contain the impact of COVID-19 on military readiness, as the virus continues to infect troops and commanders at an alarming rate. On Tuesday, the Polish government announced that General Jaroslaw Mika, who serves as general commander of Branches of the Armed Forces, had tested positive for the coronavirus. General Mika is believed to have contracted the virus during a military conference that took place in the German city of Wiesbaden, where North Atlantic Treaty Organization commanders gathered to plan an American-led military exercise.
Also on Tuesday, the United States Department of Defense said that the commander of the US Army in Europe, Lieutenant General Christopher Cavoli, participated at the Wiesbaden conference, along with several other US Army staff members. They are currently being tested for exposure to COVID-19. Meanwhile the Reuters news agency reported that the US Pentagon acknowledged that “the US military’s official tally of servicemembers and related personnel who have been infected by the coronavirus likely undercounts the actual total”. Sources told the news agency that the low age and good health of American troops was “a mixed blessing of sorts”, since it allows US servicemembers to survive the virus but at the same time reduces their symptoms that would normally trigger testing for COVID-19.
The government of Taiwan said on Tuesday that over 400 members of its armed forces had entered self-imposed quarantine in order to prevent a possible COVID-19 outbreak among military personnel. This brings the total number of Taiwanese servicemembers who are currently in quarantine to over 2,000, which includes two generals. The country’s Minister of Defense, Yen De-fa, insisted on Tuesday that the virus had not impacted Taiwan’s military readiness.
Chinese officials have not provided information about the effect of the coronavirus on the country’s military. The Chinese-language website of The Epoch Times said last week that, according to unnamed insiders, the Chinese People’s Liberation Army had “forcibly isolated” tens of thousands of servicemembers this month. There are no reports of specific numbers in the Chinese media or non-Chinese news outlets.
Finally, according to Daily NK, a South Korean website that specializes on news from North Korea, approximately 180 North Korean soldiers have died as a result of contracting COVID-19 in the past month. The website cited “a source inside the North Korean military”, who said that Pyongyang had forcibly quarantined at around 3,700 soldiers of all ranks to prevent the spread of COVID-19 in the country’s military.
► Author: Joseph Fitsanakis | Date: 10 March 2020 | Permalink
 An Android application developed by the Iranian government to assist in coordinating the country’s response to the COVID-19 epidemic has been removed by Google amidst accusations that it may be used to track Iranian dissidents. The application, named AC19, was released several days ago by Iran’s Ministry of Health and Medical Education. Its release was announced through a text message sent by the Iranian government to every mobile telephone subscriber in the country. The text message urged citizens to download the application through a dedicated website or third-party app stores, including the Google Play Store. Millions have since done so.
An Android application developed by the Iranian government to assist in coordinating the country’s response to the COVID-19 epidemic has been removed by Google amidst accusations that it may be used to track Iranian dissidents. The application, named AC19, was released several days ago by Iran’s Ministry of Health and Medical Education. Its release was announced through a text message sent by the Iranian government to every mobile telephone subscriber in the country. The text message urged citizens to download the application through a dedicated website or third-party app stores, including the Google Play Store. Millions have since done so. The United States Department of Defense has insisted that it can continue to function uninterrupted, despite claims by some media outlets that American military readiness may soon begin to degrade as a result of the coronavirus (COVID-19) outbreak.
The United States Department of Defense has insisted that it can continue to function uninterrupted, despite claims by some media outlets that American military readiness may soon begin to degrade as a result of the coronavirus (COVID-19) outbreak. A leading Chinese cybersecurity firm has accused the United States Central Intelligence Agency of using sophisticated malicious software to hack into computers belonging to the Chinese government and private sector for over a decade.
A leading Chinese cybersecurity firm has accused the United States Central Intelligence Agency of using sophisticated malicious software to hack into computers belonging to the Chinese government and private sector for over a decade. Switzerland’s Federal Department of Finance has filed a criminal complaint “against persons unknown” over media reports that a leading Swiss-based cryptological equipment manufacturer was secretly owned by the United States Central Intelligence Agency (CIA).
Switzerland’s Federal Department of Finance has filed a criminal complaint “against persons unknown” over media reports that a leading Swiss-based cryptological equipment manufacturer was secretly owned by the United States Central Intelligence Agency (CIA).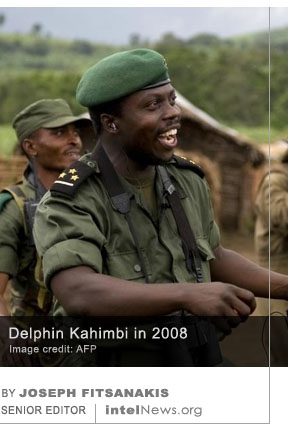 The head of military intelligence of the Democratic Republic of the Congo was found dead on Friday, just hours before he was due to testify before the country’s National Security Council. General Delphin Kahimbi, Deputy Chief of Staff of the DRC Armed Forces, and director of its military intelligence wing, was facing accusations of involvement in an alleged plot to depose the country’s new President, Félix Tshisekedi.
The head of military intelligence of the Democratic Republic of the Congo was found dead on Friday, just hours before he was due to testify before the country’s National Security Council. General Delphin Kahimbi, Deputy Chief of Staff of the DRC Armed Forces, and director of its military intelligence wing, was facing accusations of involvement in an alleged plot to depose the country’s new President, Félix Tshisekedi. United States intelligence agencies are using “a wide range” of tools, ranging from open-source collection to communications interception and human intelligence, to collect desperately needed data about the spread of the coronavirus, according to sources. As of late last week, some of the most dependable data on the spread of the virus, known as COVID-19, came from military channels of information,
United States intelligence agencies are using “a wide range” of tools, ranging from open-source collection to communications interception and human intelligence, to collect desperately needed data about the spread of the coronavirus, according to sources. As of late last week, some of the most dependable data on the spread of the virus, known as COVID-19, came from military channels of information,  An imminent peace agreement between the United States government and the Taliban will inadvertently empower the Islamic State in Afghanistan, according to a number of insiders, who warn that the soon-to-be-announced deal may have grave unintended consequences for the war-ravaged country.
An imminent peace agreement between the United States government and the Taliban will inadvertently empower the Islamic State in Afghanistan, according to a number of insiders, who warn that the soon-to-be-announced deal may have grave unintended consequences for the war-ravaged country.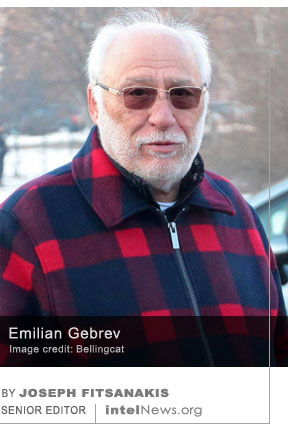 A Russian intelligence officer, who was allegedly involved in an attempt to kill a Bulgarian arms dealer in Sofia in 2015, is now a diplomat, according to report published on Tuesday by the investigative website Bellingcat. The website also claimed that there is a possible connection between the intelligence officer and the
A Russian intelligence officer, who was allegedly involved in an attempt to kill a Bulgarian arms dealer in Sofia in 2015, is now a diplomat, according to report published on Tuesday by the investigative website Bellingcat. The website also claimed that there is a possible connection between the intelligence officer and the  There are more foreign spies and their proxies operating today in Australia than during the height of the Cold War, according to the director of the Australian Security Intelligence Organisation (ASIO). This claim was made on Monday by Mike Burgess, who in 2019 was appointed director of the ASIO —Australia’s primary domestic security agency. Burgess added that the level of threat Australia faces from foreign espionage and other foreign interference activities is “currently unprecedented”.
There are more foreign spies and their proxies operating today in Australia than during the height of the Cold War, according to the director of the Australian Security Intelligence Organisation (ASIO). This claim was made on Monday by Mike Burgess, who in 2019 was appointed director of the ASIO —Australia’s primary domestic security agency. Burgess added that the level of threat Australia faces from foreign espionage and other foreign interference activities is “currently unprecedented”.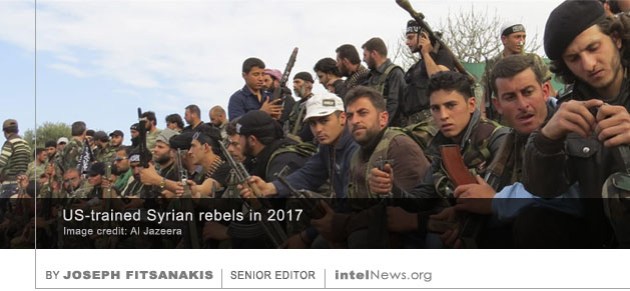 The United States government is unable to account for nearly $716 million in weapons it gave to various Syrian groups during the war against the Islamic State, according to a Department of Defense audit. The weapons were procured under the Counter Islamic State of Iraq and Syria Train and Equip Funds (CTEF) program, which was administered by the US Pentagon in 2017 and 2018. The CTEF program cost the US taxpayer a total of $930 million.
The United States government is unable to account for nearly $716 million in weapons it gave to various Syrian groups during the war against the Islamic State, according to a Department of Defense audit. The weapons were procured under the Counter Islamic State of Iraq and Syria Train and Equip Funds (CTEF) program, which was administered by the US Pentagon in 2017 and 2018. The CTEF program cost the US taxpayer a total of $930 million. The United States Federal Bureau of Investigation has arrested a Mexican man, who is accused of spying in the city of Miami on behalf of the Russian government. Local media reports suggest that the target of the man’s spying was a Russian defector who gave American authorities information about Russian espionage activities on US soil.
The United States Federal Bureau of Investigation has arrested a Mexican man, who is accused of spying in the city of Miami on behalf of the Russian government. Local media reports suggest that the target of the man’s spying was a Russian defector who gave American authorities information about Russian espionage activities on US soil. The Russian government sent a team of spies to Ireland to monitor undersea fiber-optic cables, which enable communications traffic between North America and Western Europe, according to a new report. The spies were allegedly sent to Ireland by the Main Directorate of the General Staff of the Russian Armed Forces, which is known in Russia as GU, and formerly as GRU.
The Russian government sent a team of spies to Ireland to monitor undersea fiber-optic cables, which enable communications traffic between North America and Western Europe, according to a new report. The spies were allegedly sent to Ireland by the Main Directorate of the General Staff of the Russian Armed Forces, which is known in Russia as GU, and formerly as GRU. Switzerland is reeling from the shock caused by revelations last week that Crypto AG, the world’s leading manufacturer or cryptologic equipment during the Cold War, whose clients included over 120 governments around the world, was a front company owned by the United States Central Intelligence Agency.
Switzerland is reeling from the shock caused by revelations last week that Crypto AG, the world’s leading manufacturer or cryptologic equipment during the Cold War, whose clients included over 120 governments around the world, was a front company owned by the United States Central Intelligence Agency.






US agencies in turf battle over classification level of COVID-19 meetings
March 12, 2020 by Joseph Fitsanakis 2 Comments
The meetings in point have been held since mid-January at a high-security conference room located at the headquarters of the Department of Health & Human Services (HHS) in Washington, DC. The HHS is largely in charge of the US government’s response to COVID-19, as it oversees several relevant agencies including the US Centers for Disease Control and Prevention. From the very beginning, the National Security Council —a White House decision-making body chaired by the president— ordered that the meetings be treated as classified. This meant that participants had to have top-secret security clearances in order to attend.
This decision allegedly excluded several government officials from these meetings, including leading US government biosurveillance and biosecurity experts who should have had a place at those meetings. “We had some very critical people who did not have security clearances who could not go”, one source said. Reuters quotes an unnamed “high level former official […] in the George W. Bush administration” who describes the decision to limit access to these discussions “about a response to a public health crisis” as “not normal”. But another government source told Reuters that the meetings were classified because they “had to do with China”. Yet another source said that the small number of participants was necessary to prevent potentially damaging leaks to the media.
Meanwhile, Time magazine alleged on Wednesday that a timely report by the Office of the Director of National Intelligence (DNI), which includes a section on pandemics, has been delayed. In previous years, the report, entitled Worldwide Threat Assessment, has warned that the world is not prepared for new strains of influenza that could prompt a pandemic. The report was scheduled to be released to Congress on February 12, but it remains unaccounted for. Members of the intelligence committees in Congress told Time that they did not expect the report to be released any time soon.
► Author: Joseph Fitsanakis | Date: 12 March 2020 | Permalink
Filed under Expert news and commentary on intelligence, espionage, spies and spying Tagged with Coronavirus, COVID-19, DNI, intelligence classification, News, US Department of Health & Human Services