Analysis: Iraq’s revenge campaign against Sunnis fuels new pro-ISIS wave
December 18, 2018 1 Comment
 A campaign of revenge by Iraq’s Shiite-dominated government against Sunni Arabs in regions once controlled by the Islamic State is aiding Islamists and fueling another rebellion in the country, according to a new report. In 2014, the meteoric rise of the Islamic State of Iraq and Syria —ISIS, later renamed to Islamic State— was largely aided by the strong belief among Iraqi Sunnis that they were second-class citizens in a Shiite-dominated Iraq. In addition to its Sunni credentials, the Islamic State was also able to appeal to Iraqi Sunnis by portraying itself as pious, efficient and trustworthy. This image was in a sharp contrast to the widespread provincial view of politicians in Baghdad as corrupt, indifferent and ineffectual. Popular support for the Islamic State among Iraq’s Sunni Arab minority took the Iraqi government by surprise and almost enabled the militant group to conquer Baghdad in 2015.
A campaign of revenge by Iraq’s Shiite-dominated government against Sunni Arabs in regions once controlled by the Islamic State is aiding Islamists and fueling another rebellion in the country, according to a new report. In 2014, the meteoric rise of the Islamic State of Iraq and Syria —ISIS, later renamed to Islamic State— was largely aided by the strong belief among Iraqi Sunnis that they were second-class citizens in a Shiite-dominated Iraq. In addition to its Sunni credentials, the Islamic State was also able to appeal to Iraqi Sunnis by portraying itself as pious, efficient and trustworthy. This image was in a sharp contrast to the widespread provincial view of politicians in Baghdad as corrupt, indifferent and ineffectual. Popular support for the Islamic State among Iraq’s Sunni Arab minority took the Iraqi government by surprise and almost enabled the militant group to conquer Baghdad in 2015.
Today, after the destruction of the Islamic State’s self-declared caliphate, Iraq’s Shiite-dominated security and intelligence services have returned to Sunni-majority regions that were once ruled by ISIS. But their systematic campaign of human-rights violations against Sunnis, whom they see as ISIS collaborators, is playing into Islamist propaganda and fueling a new wave of rebellion against Baghdad, according to a new report by the Washington-based Pulitzer Center on Crisis Reporting. The report, authored by The New Yorker staff writer Ben Taub, warns that the Iraqi government has no strategy on how to reach out to Iraq’s disaffected Sunni Arabs. Even worse, a state-sanctioned campaign of revenge and intimidation is taking place throughout western Iraq, in which “hundreds of thousands of civilians are suffering at the hands of their liberators”, says Taub.
In areas that until a few months ago were ruled by ISIS, anyone —regardless of age or sex— perceived as having previously supported ISIS is outright killed or sent to concentration camps. For Iraqi security forces, says Taub, civilians who did not flee ISIS are seen as inherently suspicious. Bearded men are often viewed as displaying evidence of ISIS support, even though the militant group had a policy of punishing any man who did not grow a beard in accordance with Quranic directives. Most of these people, says Taub, are fired from their jobs, sent to prison, or worse are executed by the dozens and even hundreds. A handful are tried in a court of law each month, but these are usually show trials with a conviction rate of 98 percent, he adds. Family members of the accused rarely show up in court, fearing immediate arrest and imprisonment, which appears to be a regular occurrence. It is “not uncommon for relatives [of accused ISIS supporters] to be rounded up by the security forces and sent to remote desert camps, where they are denied food, medical services, and access to documents”, reports Taub.
These arbitrary arrests are happening alongside an untold number of battlefield executions —many captured on video by jubilant Shiite soldiers and militia members— and killings of prisoners in detention centers. Taub quotes an anonymous senior official in the Iraqi intelligence services who says that “this is not just revenge on ISIS. It is revenge on Sunnis”. The widespread criminality and brutality of the Iraqi security and intelligence forces “plays directly into the jihadis’ narrative”, says Taub, by convincing Sunni Arabs that they “cannot live safely under a government dominated by Shiites”. Ultimately, what is at stake is “whether the Iraqi government can win over the segment of the population for whom ISIS seemed a viable alternative”, concludes Taub, and warns of the possibility of another armed rebellion against Baghdad by what is left of Iraq’s Sunni minority.
► Author: Joseph Fitsanakis | Date: 18 December 2018 | Permalink
 Intelligence and security services in France are investigating whether Russian involvement on social media and other platforms is playing a role in amplifying the so-called ‘yellow vests’ movement. Known in French as le mouvement des gilets jaunes, the campaign began online in May of this year as a popular protest against rising fuel prices and the high cost of living in France. In mid-November, the movement made its first public appearance with large demonstrations that have continued every weekend since then. Yellow vest protestors claim that tax increases are disproportionally affecting working- and middle-class people and that everyday life is becoming economically unsustainable in France. Some of the demonstrations have turned violent, and so far at least eight people have died as a result. The ensuing crisis has become the most significant threat to the government of Emmanuel Macron, as the protests are increasingly evolving into an anti-Macron rallies.
Intelligence and security services in France are investigating whether Russian involvement on social media and other platforms is playing a role in amplifying the so-called ‘yellow vests’ movement. Known in French as le mouvement des gilets jaunes, the campaign began online in May of this year as a popular protest against rising fuel prices and the high cost of living in France. In mid-November, the movement made its first public appearance with large demonstrations that have continued every weekend since then. Yellow vest protestors claim that tax increases are disproportionally affecting working- and middle-class people and that everyday life is becoming economically unsustainable in France. Some of the demonstrations have turned violent, and so far at least eight people have died as a result. The ensuing crisis has become the most significant threat to the government of Emmanuel Macron, as the protests are increasingly evolving into an anti-Macron rallies. The terrorist attack in the French city of Strasbourg on December 11 raises important security concerns for Europe’s ability to defend itself against a
The terrorist attack in the French city of Strasbourg on December 11 raises important security concerns for Europe’s ability to defend itself against a  Russia “paved the way” for last November’s seizure of Ukrainian Navy ships by launching a major cyber attack and disinformation campaign aimed at Ukraine, according to a cyber security firm and the European Union. In what has become known as the Kerch Strait incident of November 25, border service coast guard vessels belonging to the Russian Federal Security Service (FSB) opened fire on three Ukrainian Navy ships that were attempting to enter the Sea of Azov through the Kerch Strait. All three Ukrainian vessels, along with crews totaling 24 sailors, were captured by the Russian force and remain in detention. Ukraine condemned Russia’s action as an act of war and declared martial law in its eastern and southern provinces. But Moscow said the incident had been caused by a provocation by the Ukrainian government, in a desperate effort to increase its popularity at home. Meanwhile, the three Ukrainian ships and their crews remain in Russia.
Russia “paved the way” for last November’s seizure of Ukrainian Navy ships by launching a major cyber attack and disinformation campaign aimed at Ukraine, according to a cyber security firm and the European Union. In what has become known as the Kerch Strait incident of November 25, border service coast guard vessels belonging to the Russian Federal Security Service (FSB) opened fire on three Ukrainian Navy ships that were attempting to enter the Sea of Azov through the Kerch Strait. All three Ukrainian vessels, along with crews totaling 24 sailors, were captured by the Russian force and remain in detention. Ukraine condemned Russia’s action as an act of war and declared martial law in its eastern and southern provinces. But Moscow said the incident had been caused by a provocation by the Ukrainian government, in a desperate effort to increase its popularity at home. Meanwhile, the three Ukrainian ships and their crews remain in Russia. In a surprising departure from established practice, the United States Central Intelligence Agency has publicized the name of its incoming head of operations. Beth Kimber, a 34-year veteran of the Agency, will become the first woman in the CIA’s 70-year history to lead the Directorate of Operations. Officers in the Directorate of Operations, formerly known as the National Clandestine Service, spend their careers recruiting foreign agents to spy for the United States, while also carrying out covert operations around the world. This is also the first time that the CIA has chosen to publicly identify its Deputy Director for Operations —Kimber’s official title, abbreviated as DDO. Previous DDO have been undercover officers whose namse have remained undisclosed. Kimber’s promotion was
In a surprising departure from established practice, the United States Central Intelligence Agency has publicized the name of its incoming head of operations. Beth Kimber, a 34-year veteran of the Agency, will become the first woman in the CIA’s 70-year history to lead the Directorate of Operations. Officers in the Directorate of Operations, formerly known as the National Clandestine Service, spend their careers recruiting foreign agents to spy for the United States, while also carrying out covert operations around the world. This is also the first time that the CIA has chosen to publicly identify its Deputy Director for Operations —Kimber’s official title, abbreviated as DDO. Previous DDO have been undercover officers whose namse have remained undisclosed. Kimber’s promotion was  A Russian former police officer, who is serving a prison sentence in Russia for having spied for the United States Central Intelligence Agency, has written an open letter to President Donald Trump, asking to be freed. Yevgeny A. Chistov was arrested by the Russian Federal Security Service (FSB) in 2014 on charges of spying for Washington. During his trial, he admitted having been recruited by the CIA when he worked as an officer in the police, Russia’s federal law-enforcement agency, which operates under the Ministry of Internal Affairs. Russian state prosecutors accused him of having established contact with the CIA in 2011. In 2015, he was
A Russian former police officer, who is serving a prison sentence in Russia for having spied for the United States Central Intelligence Agency, has written an open letter to President Donald Trump, asking to be freed. Yevgeny A. Chistov was arrested by the Russian Federal Security Service (FSB) in 2014 on charges of spying for Washington. During his trial, he admitted having been recruited by the CIA when he worked as an officer in the police, Russia’s federal law-enforcement agency, which operates under the Ministry of Internal Affairs. Russian state prosecutors accused him of having established contact with the CIA in 2011. In 2015, he was  A report from the United States Department of Defense warns that the Islamic State is swiftly returning to its insurgent roots, as observers in Iraq and Syria caution that the group is witnessing a revival. It has been four years since the Islamic State —known then as the Islamic State of Iraq and Syria, or ISIS— conquered much of eastern Syria and more than a third of Iraq’s territory. But by the end of 2017, virtually the entirety of ISIS’ self-styled ‘caliphate’ had been obliterated by an ‘unholy alliance’ of US-backed Iraqi government forces, Iranian-supported Shiite militias, Kurdish guerillas and Western airpower.
A report from the United States Department of Defense warns that the Islamic State is swiftly returning to its insurgent roots, as observers in Iraq and Syria caution that the group is witnessing a revival. It has been four years since the Islamic State —known then as the Islamic State of Iraq and Syria, or ISIS— conquered much of eastern Syria and more than a third of Iraq’s territory. But by the end of 2017, virtually the entirety of ISIS’ self-styled ‘caliphate’ had been obliterated by an ‘unholy alliance’ of US-backed Iraqi government forces, Iranian-supported Shiite militias, Kurdish guerillas and Western airpower. The daughter of the founder of Huawei Technologies, one of the world’s leading telecommunications hardware manufacturers, has been arrested in Canada, reportedly at the request of the United States. Meng Wanzhou (pictured, also known as Sabrina Meng) serves as Huawei’s deputy chair and chief financial officer. She is the daughter of Ren Zhengfei a former officer in the Chinese People’s Liberation Army, who established the company in 1988 and has since amassed a personal fortune estimated at $3.5 billion. By virtue of her family background and position in Huawei, Meng is often
The daughter of the founder of Huawei Technologies, one of the world’s leading telecommunications hardware manufacturers, has been arrested in Canada, reportedly at the request of the United States. Meng Wanzhou (pictured, also known as Sabrina Meng) serves as Huawei’s deputy chair and chief financial officer. She is the daughter of Ren Zhengfei a former officer in the Chinese People’s Liberation Army, who established the company in 1988 and has since amassed a personal fortune estimated at $3.5 billion. By virtue of her family background and position in Huawei, Meng is often  The main domestic intelligence agency of the Czech Republic has accused Russia of “the most serious wave of cyberespionage” to target the country in recent years. The claim was made on Monday in Prague by the Security Information Service (BIS), the primary domestic national intelligence agency of the Czech Republic. Details of the alleged cyberespionage plot are included in the BIS’
The main domestic intelligence agency of the Czech Republic has accused Russia of “the most serious wave of cyberespionage” to target the country in recent years. The claim was made on Monday in Prague by the Security Information Service (BIS), the primary domestic national intelligence agency of the Czech Republic. Details of the alleged cyberespionage plot are included in the BIS’ 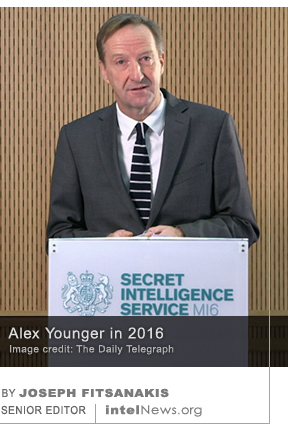 The director of Britain’s Secret Intelligence Service —known as MI6— has outlined the parameters of a new, “fourth generation of espionage”, which he said is needed to combat the “threats of the hybrid age”. Alex Younger, 55, is a career intelligence officer who joined MI6 in 1991, after serving in the British Army. He served as chief of global operations —considered the number two position at MI6— before being
The director of Britain’s Secret Intelligence Service —known as MI6— has outlined the parameters of a new, “fourth generation of espionage”, which he said is needed to combat the “threats of the hybrid age”. Alex Younger, 55, is a career intelligence officer who joined MI6 in 1991, after serving in the British Army. He served as chief of global operations —considered the number two position at MI6— before being  Saudi Crown Prince Mohammed bin Salman sent at least eleven text messages to the man in charge of the 15-member hit team that killed journalist Jamal Khashoggi last month, according to a classified report produced by the United States Central Intelligence Agency. The CIA report was leaked to The Wall Street Journal, which said in a
Saudi Crown Prince Mohammed bin Salman sent at least eleven text messages to the man in charge of the 15-member hit team that killed journalist Jamal Khashoggi last month, according to a classified report produced by the United States Central Intelligence Agency. The CIA report was leaked to The Wall Street Journal, which said in a  The United States government plan to impose tighter visa restrictions and wider background checks on Chinese nationals studying at American universities, over espionage concerns. The news follows reports earlier this year that the administration of US President Donald Trump considered banning all Chinese nationals from studying at American universities. In October of this year, The Financial Times
The United States government plan to impose tighter visa restrictions and wider background checks on Chinese nationals studying at American universities, over espionage concerns. The news follows reports earlier this year that the administration of US President Donald Trump considered banning all Chinese nationals from studying at American universities. In October of this year, The Financial Times  The Australian government has proposed a new law that would give intelligence officers broader powers to use firearms during undercover operations abroad. If it is approved by parliament, the new law would apply to the Australian Secret Intelligence Service (ASIS), a civilian intelligence agency that carries out covert and clandestine operations abroad. Modeled after Britain’s Secret Intelligence Service (MI6), ASIS was established in 1952, but its existence was not officially acknowledged by the Australian government until 25 years later, in 1977.
The Australian government has proposed a new law that would give intelligence officers broader powers to use firearms during undercover operations abroad. If it is approved by parliament, the new law would apply to the Australian Secret Intelligence Service (ASIS), a civilian intelligence agency that carries out covert and clandestine operations abroad. Modeled after Britain’s Secret Intelligence Service (MI6), ASIS was established in 1952, but its existence was not officially acknowledged by the Australian government until 25 years later, in 1977. A senior North Korea expert in the United States Central Intelligence Agency, who has been instrumental in the ongoing negotiations between Washington and Pyongyang, has tendered his resignation, according to sources. The official was
A senior North Korea expert in the United States Central Intelligence Agency, who has been instrumental in the ongoing negotiations between Washington and Pyongyang, has tendered his resignation, according to sources. The official was 






Details of Albania’s clandestine operatives posted online due to admin error
December 19, 2018 Leave a comment
Until the end of the Cold War, Albania was a communist state aligned with China. Since 1991, however, the former communist country has tried to align itself with the West. As part of this strategy, successive Albanian administrations have tried to combat widespread nepotism and government corruption. A significant aspect of this ongoing anti-corruption campaign involves the daily publication of the financial activities of Albanian government agencies. This information is available in searchable spreadsheets on the website of Albania’s Ministry of Finance and Economy. Recently, however, Vincent Triest, a researcher with British-based investigative website Bellingcat, noticed that the publicly available spreadsheets contained information about the State Intelligence Service, Albania’s spy agency, known as SHISH. In reading through the spreadsheets, Triest was able to find the names, official job titles, salaries and monthly expenses of at least eight senior members of SHISH. Most of them, said Triest, serve under official (diplomatic) cover at Albanian embassies and consulates in Greece, Italy, Belgium, Serbia, and elsewhere in Europe.
In a follow-up article posted yesterday on Bellingcat’s website, Triest said that the spreadsheets on the website of the Albanian Finance Ministry contain names and national identification records of SHISH officers, the agency field offices where they are serving, and even the make and model of the vehicles they drive along with their license plate numbers. A separate spreadsheet lists the construction contractors, plumbers and electricians used by various SHISH field offices, as well as the mechanics that are contracted to service the agency’s vehicles. Remarkably, at least two of the exposed SHISH officers are serving in “sensitive posts at NATO headquarters in Brussels”, writes Triest. This has raised alarms at NATO, as Albanian intelligence officers with access to NATO’s secrets could now become susceptible to possible recruitment by adversary spy agencies, said The Independent. The paper added that it notified the Albanian government of the security breach, and was told that the sensitive data would be promptly removed from government websites.
► Author: Joseph Fitsanakis | Date: 19 December 2018 | Permalink
Filed under Expert news and commentary on intelligence, espionage, spies and spying Tagged with Albania, NATO, News, SHISH (Albania), State Intelligence Service (Albania)