Swiss trying to change image as Europe’s spy hub, say officials
February 6, 2018 4 Comments
 Officials in Switzerland say new laws enacted in recent months will help them change their country’s image as one of Europe’s most active spy venues. For decades, the small alpine country has been a destination of choice for intelligence officers from all over the world, who use it as a place to meet assets from third countries. For example, a case officer from Britain’s Secret Intelligence Service (MI6) will travel to Switzerland to meet her Algerian agent. She will exchange money and documents with him before she returns to Britain and he to Algeria, presumably after depositing his earnings into a Swiss bank account.
Officials in Switzerland say new laws enacted in recent months will help them change their country’s image as one of Europe’s most active spy venues. For decades, the small alpine country has been a destination of choice for intelligence officers from all over the world, who use it as a place to meet assets from third countries. For example, a case officer from Britain’s Secret Intelligence Service (MI6) will travel to Switzerland to meet her Algerian agent. She will exchange money and documents with him before she returns to Britain and he to Algeria, presumably after depositing his earnings into a Swiss bank account.
There are multiple reasons that explain Switzerland’s preferred status as a meeting place for spies and their handlers. The country is suitably located in the center of Europe and is a member of the European Union’s Schengen Treaty, which means that a passport is not required to enter it when arriving there from European Union member-states. Additionally, the country features an efficient transportation and telecommunication infrastructure, and its stable political system offers predictability and security, despite the limited size and strength of its law enforcement and security agencies. Perhaps most important of all, the Swiss have learned not to ask questions of visitors, many of whom flock to the country to entrust their cash to its privacy-conscious banking sector.
But, according to the Swiss Federal Intelligence Service (FIS), foreign spies and their handlers should find another venue to meet in secret. Speaking to the Sunday edition of Switzerland’s NZZ newspaper, FIS spokeswoman Isabelle Graber said she and her colleagues were aware that their country is a venue for meetings between intelligence operatives from third countries. Such meetings have “continued to rise in the last few years” and include “everyone from security agency employees to freelancers”, as “the market in trading secrets has exploded”, she said. That trend, added Graber, has led to a corresponding rise in meetings aimed at exchanging information for money. Many such meetings take place throughout Switzerland, she noted, and are “in violation of Swiss sovereignty and can lead to operations against the interests of the nation”.
In the past, said Graber, FIS was unable to prevent such activities on Swiss soil, due to pro-privacy legislation, which meant that the agency’s ability to combat foreign espionage in Switzerland was “far more limited than in other countries”. However, said the intelligence agency spokeswoman, the law recently changed to permit FIS to break into homes and hotels, hack into computers, wiretap phones, and implement surveillance on individuals believed to be spies or intelligence officers of foreign countries. Armed with the new legislation, the FIS is now “working hard to clear up third-country meetings [and] to prevent these from happening or at least disrupt them”, said Graber. Several times this year alone, FIS had forward information about “third-country meetings” to judicial authorities in Switzerland, she said.
► Author: Ian Allen | Date: 06 February 2018 | Permalink
 North Korea used its embassy in Berlin to acquire technologies that were almost certainly used to advance its missile and nuclear weapons programs, according to the head of Germany’s counterintelligence agency. For many decades, Pyongyang has used a sophisticated international system of procurement to acquire technologies and material for its conventional and nuclear weapons programs. These secret methods have enabled the country to evade sanctions placed on it by the international community, which wants to foil North Korea’s nuclear aspirations.
North Korea used its embassy in Berlin to acquire technologies that were almost certainly used to advance its missile and nuclear weapons programs, according to the head of Germany’s counterintelligence agency. For many decades, Pyongyang has used a sophisticated international system of procurement to acquire technologies and material for its conventional and nuclear weapons programs. These secret methods have enabled the country to evade sanctions placed on it by the international community, which wants to foil North Korea’s nuclear aspirations. Foreign intelligence collection and espionage threats against Australia are greater today than at any time during the Cold War, according to a senior Australian intelligence official. The claim was made on Wednesday by Peter Vickery, deputy director general of the Australian Security Intelligence Organisation (ASIO), the country’s primary counterintelligence agency. He was speaking before a parliamentary committee that is considering aspects of a proposed bill, which aims to combat foreign influence on Australian political and economic life. If enacted, the bill would require anyone who is professionally advocating or campaigning in favor of “foreign entities” to register with the government. Several opposition parties and groups, including the Catholic Church, have
Foreign intelligence collection and espionage threats against Australia are greater today than at any time during the Cold War, according to a senior Australian intelligence official. The claim was made on Wednesday by Peter Vickery, deputy director general of the Australian Security Intelligence Organisation (ASIO), the country’s primary counterintelligence agency. He was speaking before a parliamentary committee that is considering aspects of a proposed bill, which aims to combat foreign influence on Australian political and economic life. If enacted, the bill would require anyone who is professionally advocating or campaigning in favor of “foreign entities” to register with the government. Several opposition parties and groups, including the Catholic Church, have  The Taliban have an open and constant presence in 70 percent of Afghanistan, according to an extensive study undertaken by the BBC, which was conducted over several months in every corner of the country. The report comes nearly 17 years after a military coalition led by the United States invaded Afghanistan in response to the attacks of September 11, 2001. Since then, Western forces, most of them members of the North Atlantic Treaty Organization, have spent countless lives and billions of dollars in an effort to defeat the Pashtun-led insurgency of the Taliban. American forces in the country, which at the end of 2009 numbered close to 100,000 troops, were reduced to a force of fewer than 8,000 by 2014, when US President Barack Obama declared the war over.
The Taliban have an open and constant presence in 70 percent of Afghanistan, according to an extensive study undertaken by the BBC, which was conducted over several months in every corner of the country. The report comes nearly 17 years after a military coalition led by the United States invaded Afghanistan in response to the attacks of September 11, 2001. Since then, Western forces, most of them members of the North Atlantic Treaty Organization, have spent countless lives and billions of dollars in an effort to defeat the Pashtun-led insurgency of the Taliban. American forces in the country, which at the end of 2009 numbered close to 100,000 troops, were reduced to a force of fewer than 8,000 by 2014, when US President Barack Obama declared the war over. Chinese spies hacked the computer servers of the African Union headquarters in the Ethiopian capital Addis Ababa, which the Chinese government funded and built as a gift to the organization, a French newspaper has claimed. Beijing donated $200 million toward the project and hired the state-owned China State Construction Engineering Corporation to build the tower, which was
Chinese spies hacked the computer servers of the African Union headquarters in the Ethiopian capital Addis Ababa, which the Chinese government funded and built as a gift to the organization, a French newspaper has claimed. Beijing donated $200 million toward the project and hired the state-owned China State Construction Engineering Corporation to build the tower, which was  Dutch spies identified a notorious Russian hacker group that compromised computer servers belonging to the Democratic Party of the United States and notified American authorities of the attack, according to reports. In 2016, US intelligence agencies determined that a Russian hacker group known as Cozy Bear, or APT29, led a concerted effort to interfere in the US presidential election. The effort, which according to US intelligence agencies was sponsored by the Russian government, involved cyber-attacks against computer systems in the White House and the Department of State, among other targets. It also involved the theft of thousands of emails from computer servers belonging to the Democratic National Committee, which is the governing body of the Democratic Party. The stolen emails were eventually leaked to WikiLeaks, DCLeaks, and other online outlets. Prior descriptions of the Russian hacking in the media have hinted that US intelligence agencies were notified of the Russian cyber-attacks by foreign spy agencies. But there was no mention of where the initial clues came from.
Dutch spies identified a notorious Russian hacker group that compromised computer servers belonging to the Democratic Party of the United States and notified American authorities of the attack, according to reports. In 2016, US intelligence agencies determined that a Russian hacker group known as Cozy Bear, or APT29, led a concerted effort to interfere in the US presidential election. The effort, which according to US intelligence agencies was sponsored by the Russian government, involved cyber-attacks against computer systems in the White House and the Department of State, among other targets. It also involved the theft of thousands of emails from computer servers belonging to the Democratic National Committee, which is the governing body of the Democratic Party. The stolen emails were eventually leaked to WikiLeaks, DCLeaks, and other online outlets. Prior descriptions of the Russian hacking in the media have hinted that US intelligence agencies were notified of the Russian cyber-attacks by foreign spy agencies. But there was no mention of where the initial clues came from. ►►This website has
►►This website has  The British government has announced that it will form a new intelligence unit tasked with preventing the spread of so-called “fake news” by foreign states, including Russia. The decision was revealed earlier this week in London by a government spokesman, who said that the new unit will be named “National Security Communications Unit”. The spokesman added that the unit will be responsible for “combating disinformation by state actors and others”. When asked by reporters whether the effort was meant as a response to the phenomenon often described as “fake news”, the spokesman said that it was.
The British government has announced that it will form a new intelligence unit tasked with preventing the spread of so-called “fake news” by foreign states, including Russia. The decision was revealed earlier this week in London by a government spokesman, who said that the new unit will be named “National Security Communications Unit”. The spokesman added that the unit will be responsible for “combating disinformation by state actors and others”. When asked by reporters whether the effort was meant as a response to the phenomenon often described as “fake news”, the spokesman said that it was. A former director of Bulgaria’s intelligence service, who headed the agency for nearly a decade, has been jailed for embezzling millions of dollars from public funds. General Kircho Kirov, 67, was director of the Bulgarian National Intelligence Service (NIS) from February 2003 until January 2012. After stepping down from his post he was appointed national security advisor to Bulgaria’s Prime Minister, Boiko Borissov. But he soon fell out with Borrisov and was fired after just two months on the job. Now Borissov’s administration has
A former director of Bulgaria’s intelligence service, who headed the agency for nearly a decade, has been jailed for embezzling millions of dollars from public funds. General Kircho Kirov, 67, was director of the Bulgarian National Intelligence Service (NIS) from February 2003 until January 2012. After stepping down from his post he was appointed national security advisor to Bulgaria’s Prime Minister, Boiko Borissov. But he soon fell out with Borrisov and was fired after just two months on the job. Now Borissov’s administration has  Media reports from Lebanon claim that Israel was behind a
Media reports from Lebanon claim that Israel was behind a 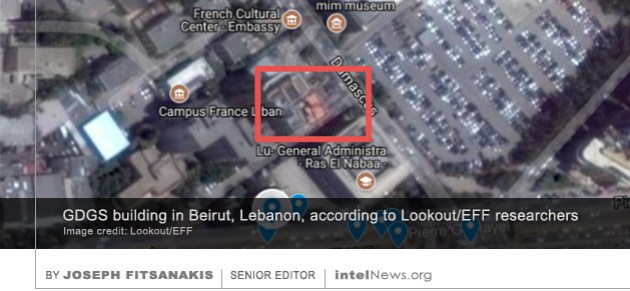 The spy agency of Lebanon used a virus designed for the Android mobile operating system to compromise the cell phones of thousands of people in at least 20 countries, according to a new mobile security report. The 50-page
The spy agency of Lebanon used a virus designed for the Android mobile operating system to compromise the cell phones of thousands of people in at least 20 countries, according to a new mobile security report. The 50-page  A former case officer in the Central Intelligence Agency, who was arrested this week for violating the United States Espionage Act, was lured back to America from Hong Kong at least once by counterintelligence investigators, according to reports. Jerry Chun Shing Lee, 53, served in the CIA from 1994 to 2007. He was
A former case officer in the Central Intelligence Agency, who was arrested this week for violating the United States Espionage Act, was lured back to America from Hong Kong at least once by counterintelligence investigators, according to reports. Jerry Chun Shing Lee, 53, served in the CIA from 1994 to 2007. He was  A former operations officer in the United States Central Intelligence Agency has been arrested on charges of illegally possessing top secret information, including lists of real names of foreign assets and addresses of CIA safe houses. The news emerged on Tuesday, as the US Department of Justice announced that the Federal Bureau of Investigation had filed a criminal complaint over the weekend. The complaint identifies the former case officer as Jerry Chun Shing Lee, also known as Zhen Cheng Li. Lee, a 53-year-old naturalized American, served in the CIA from 1994 to 2007 “in various overseas positions and locations”, according to court documents. Lee has
A former operations officer in the United States Central Intelligence Agency has been arrested on charges of illegally possessing top secret information, including lists of real names of foreign assets and addresses of CIA safe houses. The news emerged on Tuesday, as the US Department of Justice announced that the Federal Bureau of Investigation had filed a criminal complaint over the weekend. The complaint identifies the former case officer as Jerry Chun Shing Lee, also known as Zhen Cheng Li. Lee, a 53-year-old naturalized American, served in the CIA from 1994 to 2007 “in various overseas positions and locations”, according to court documents. Lee has  A delegation of Syrian rebels is currently in Washington to ask that that United States President Donald Trump authorizes the Central Intelligence Agency to resume giving them military assistance. In 2013, the then-US President Barack Obama instructed the CIA to provide covert support to fighters in Syria. The CIA promptly began to assist fighters affiliated with the Free Syrian Army (FSA), whose goal was to topple the regime of Syrian President Bashar al-Assad. Under the project, which was codenamed TIMBER SYCAMORE, CIA personnel trained FSA fighters and gave them light weaponry. But in July of last year, President Trump
A delegation of Syrian rebels is currently in Washington to ask that that United States President Donald Trump authorizes the Central Intelligence Agency to resume giving them military assistance. In 2013, the then-US President Barack Obama instructed the CIA to provide covert support to fighters in Syria. The CIA promptly began to assist fighters affiliated with the Free Syrian Army (FSA), whose goal was to topple the regime of Syrian President Bashar al-Assad. Under the project, which was codenamed TIMBER SYCAMORE, CIA personnel trained FSA fighters and gave them light weaponry. But in July of last year, President Trump 






Ex-spy chief claims Palestinian officials worked with CIA to wiretap opponents
February 7, 2018 by Joseph Fitsanakis 1 Comment
The leaked document appears to show that the Palestinian Preventive Security Service reached out to the CIA in 2013 asking for assistance with installing a communications surveillance system in the West Bank. The CIA agreed to provide the system in exchange for access to the intercepted data. The two agencies installed the interception system in the summer of 2014 and initiated what appears to have been a large-scale operation that included thousands of telephone subscribers. Initial targets of the operation included members of Hamas —the Palestinian group that controls the Gaza Strip— as well as members of the Iran-supported Islamic Jihad Movement in Palestine. But, according to the Associated Press, over time the targets of the program expanded to include “thousands of Palestinians, from senior figures in militant groups to judges, lawyers, civic leaders and political allies of Abbas”. The list of targets included Tirawi and Obeidat, who filed the official complaint on Tuesday.
The anonymous leaker of the document said he decided to quit his job and reveal the information about the intercepts after US President Donald Trump shifted Washington’s policy on Israel’s capital, by officially recognizing Jerusalem as the capital of the Jewish state. Earlier in February, the Palestinian Authority dismissed the leaked document as “nonsense” and said it was part of a large conspiracy that sought to harm Palestinian interests. The CIA refused to comment on the allegations.
► Author: Joseph Fitsanakis | Date: 07 February 2018 | Permalink
Filed under Expert news and commentary on intelligence, espionage, spies and spying Tagged with CIA, Jawad Obeidat, News, Palestine, Palestinian Authority, Palestinian General Intelligence, Palestinian Preventive Security Service, Tawifq Tirawi, United States